
Spam (electronic)
Encyclopedia
Electronic messaging
Electronic messaging may refer to:One to One communication*Instant message *Personal message *Text message *SMTP *Email...
systems (including most broadcast media, digital delivery systems) to send unsolicited bulk messages indiscriminately. While the most widely recognized form of spam is e-mail spam
E-mail spam
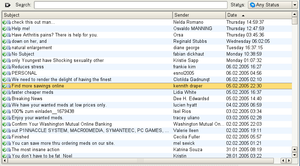
Email spam, also known as junk email or unsolicited bulk email , is a subset of spam that involves nearly identical messages sent to numerous recipients by email. Definitions of spam usually include the aspects that email is unsolicited and sent in bulk. One subset of UBE is UCE...
, the term is applied to similar abuses in other media: instant messaging spam
Messaging spam
Messaging spam, sometimes called SPIM,is a type of spam targeting users of instant messaging services.-Instant messaging applications:...
, Usenet newsgroup spam
Newsgroup spam
Newsgroup spam is a type of spam where the targets are Usenet newsgroups.Spamming of Usenet newsgroups actually pre-dates e-mail spam. The first widely recognized Usenet spam was posted on 18 January 1994 by Clarence L. Thomas IV, a sysadmin at Andrews University...
, Web search engine spam
Spamdexing
In computing, spamdexing is the deliberate manipulation of search engine indexes...
, spam in blogs
Spam in blogs
Spam in blogs is a form of spamdexing. It is done by automatically posting random comments or promoting commercial services to blogs, wikis, guestbooks, or other publicly...
, wiki spam, online classified ads
Classified advertising
Classified advertising is a form of advertising which is particularly common in newspapers, online and other periodicals which may be sold or distributed free of charge...
spam, mobile phone messaging spam
Mobile phone spam
Mobile phone spam is a form of spamming directed at the text messaging service of a mobile phone. It is described as mobile spamming, SMS spam, text spam or m-spam....
, Internet forum spam
Forum spam
Forum spam is the creating of messages that are advertisements, abusive, or otherwise unwanted on Internet forums. It is generally done by automated spambots.- Types of spam :...
, junk fax transmissions
Junk fax
Junk faxes are a form of telemarketing where unsolicited advertisements are sent via fax transmission. Junk faxes are the faxed equivalent of spam or junk mail...
, social networking spam, television advertising
Advertising
Advertising is a form of communication used to persuade an audience to take some action with respect to products, ideas, or services. Most commonly, the desired result is to drive consumer behavior with respect to a commercial offering, although political and ideological advertising is also common...
and file sharing network spam.
Spamming remains economically viable because advertisers have no operating costs beyond the management of their mailing lists, and it is difficult to hold senders accountable for their mass mailings. Because the barrier to entry
Barriers to entry
In theories of competition in economics, barriers to entry are obstacles that make it difficult to enter a given market. The term can refer to hindrances a firm faces in trying to enter a market or industry - such as government regulation, or a large, established firm taking advantage of economies...
is so low, spammers are numerous, and the volume of unsolicited mail has become very high. In the year 2011, the estimated figure for spam messages is around seven trillion. The costs, such as lost productivity and fraud, are borne by the public and by Internet service provider
Internet service provider
An Internet service provider is a company that provides access to the Internet. Access ISPs directly connect customers to the Internet using copper wires, wireless or fiber-optic connections. Hosting ISPs lease server space for smaller businesses and host other people servers...
s, which have been forced to add extra capacity to cope with the deluge. Spamming has been the subject of legislation in many jurisdictions.
A person who creates electronic spam is called a spammer.
Increasingly, email spam today is sent via "zombie
Zombie computer
In computer science, a zombie is a computer connected to the Internet that has been compromised by a cracker, computer virus or trojan horse and can be used to perform malicious tasks of one sort or another under remote direction. Botnets of zombie computers are often used to spread e-mail spam...
networks", networks of virus
Computer virus
A computer virus is a computer program that can replicate itself and spread from one computer to another. The term "virus" is also commonly but erroneously used to refer to other types of malware, including but not limited to adware and spyware programs that do not have the reproductive ability...
- or worm
Computer worm
A computer worm is a self-replicating malware computer program, which uses a computer network to send copies of itself to other nodes and it may do so without any user intervention. This is due to security shortcomings on the target computer. Unlike a computer virus, it does not need to attach...
-infected personal computers in homes and offices around the globe; many modern worms install a backdoor which allows the spammer access to the computer and use it for malicious purposes. This complicates attempts to control the spread of spam, as in many cases the spam doesn't obviously originate from the spammer. In November 2008 an ISP, McColo
McColo
McColo was a San Jose-based web hosting service provider. In late 2008, the company was shut down by the two upstream providers, Global Crossing and Hurricane Electric, because a significant amount of malware and botnets had been trafficking from the McColo servers.-History:McColo was formed by a...
, which was providing service to botnet
Botnet
A botnet is a collection of compromised computers connected to the Internet. Termed "bots," they are generally used for malicious purposes. When a computer becomes compromised, it becomes a part of a botnet...
operators, was depeered and spam dropped 50%-75% Internet-wide. At the same time, it is becoming clear that malware
Malware
Malware, short for malicious software, consists of programming that is designed to disrupt or deny operation, gather information that leads to loss of privacy or exploitation, or gain unauthorized access to system resources, or that otherwise exhibits abusive behavior...
authors, spammers, and phishers
Phishing
Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT...
are learning from each other, and possibly forming various kinds of partnerships.
An industry of email address harvesting is dedicated to collecting email addresses and selling compiled databases. Some of these address harvesting approaches rely on users not reading the fine print of agreements, resulting in them agreeing to send messages indiscriminately to their contacts. This is a common approach in social networking spam
Social networking spam
Social networking spam is spam directed at users of internet social networking services such as MySpace, Facebook or LinkedIn. Users of social networking services can send notes, that may include embedded links to other social network locations or even outside sites, to one another.This is where...
such as that generated by the social networking site Quechup
Quechup
Quechup is a social networking website that came to prominence in 2007 when it used automatic email invitations for viral marketing to all the e-mail addresses in its members address books...
.
Instant Messaging
Instant Messaging spam makes use of instant messagingInstant messaging
Instant Messaging is a form of real-time direct text-based chatting communication in push mode between two or more people using personal computers or other devices, along with shared clients. The user's text is conveyed over a network, such as the Internet...
systems. Although less ubiquitous than its e-mail counterpart, according to a report from Ferris Research, 500 million spam IMs were sent in 2003, twice the level of 2002. As instant messaging tends to not be blocked by firewalls, it is an especially useful channel for spammers. This is very common on many instant messaging systems such as Skype
Skype
Skype is a software application that allows users to make voice and video calls and chat over the Internet. Calls to other users within the Skype service are free, while calls to both traditional landline telephones and mobile phones can be made for a fee using a debit-based user account system...
.
Newsgroup and forum
Newsgroup spam is a type of spam where the targets are Usenet newsgroups. Spamming of Usenet newsgroups actually pre-dates e-mail spam. Usenet convention defines spamming as excessive multiple posting, that is, the repeated posting of a message (or substantially similar messages). The prevalence of Usenet spam led to the development of the Breidbart IndexBreidbart Index
The Breidbart Index, developed by Seth Breidbart, is the most significant cancel index in Usenet.A cancel index measures the dissemination intensity of substantively identical articles. If the index exceeds a threshold the articles are called newsgroup spam...
as an objective measure of a message's "spamminess".
Forum spam is the creating of messages that are advertisements on Internet forums. It is generally done by automated spambots. Most forum spam consists of links to external sites, with the dual goals of increasing search engine visibility in highly competitive areas such as weight loss, pharmaceuticals, gambling, pornography, real estate or loans, and generating more traffic for these commercial websites. Some of these links contain code to track the spambot's identity; if a sale goes through, when the spammer behind the spambot works on commission.
Mobile phone
Mobile phone spam is directed at the text messagingText messaging
Text messaging, or texting, refers to the exchange of brief written text messages between fixed-line phone or mobile phone and fixed or portable devices over a network...
service of a mobile phone
Mobile phone
A mobile phone is a device which can make and receive telephone calls over a radio link whilst moving around a wide geographic area. It does so by connecting to a cellular network provided by a mobile network operator...
. This can be especially irritating to customers not only for the inconvenience but also because of the fee they may be charged per text message received in some markets.
The term "SpaSMS" was coined at the adnews website Adland in 2000 to describe spam SMS.
Online game messaging
Many online games allow players to contact each other via player-to-player messaging, chat rooms, or public discussion areas. What qualifies as spam varies from game to game, but usually this term applies to all forms of message flooding, violating the terms of service contract for the website. This is particularly common in MMORPGs where the spammers are trying to sell game-related "items" for real-world money, chiefly among these items is in-game currency.Spam targeting search engines (spamdexing)
Spamdexing (a portmanteau of spamming and indexing) refers to a practice on the World Wide WebWorld Wide Web
The World Wide Web is a system of interlinked hypertext documents accessed via the Internet...
of modifying HTML
HTML
HyperText Markup Language is the predominant markup language for web pages. HTML elements are the basic building-blocks of webpages....
pages to increase the chances of them being placed high on search engine
Web search engine
A web search engine is designed to search for information on the World Wide Web and FTP servers. The search results are generally presented in a list of results often referred to as SERPS, or "search engine results pages". The information may consist of web pages, images, information and other...
relevancy lists. These sites use "black hat search engine optimization
Search engine optimization
Search engine optimization is the process of improving the visibility of a website or a web page in search engines via the "natural" or un-paid search results...
(SEO) techniques" to deliberately manipulate their rank in search engines. Many modern search engines modified their search algorithms to try to exclude web pages utilizing spamdexing tactics. For example, the search bots will detect repeated keywords as spamming by using a grammar analysis. If a website owner is found to have spammed the webpage to falsely increase its page rank, the website may be penalized by search engines.
Blog, wiki, and guestbook
Blog spam, or "blam" for short, is spamming on weblogsBlog
A blog is a type of website or part of a website supposed to be updated with new content from time to time. Blogs are usually maintained by an individual with regular entries of commentary, descriptions of events, or other material such as graphics or video. Entries are commonly displayed in...
. In 2003, this type of spam took advantage of the open nature of comments in the blogging software Movable Type
Movable Type
Movable Type is a weblog publishing system developed by the company Six Apart. It was publicly announced on September 3, 2001; version 1.0 was publicly released on October 8, 2001. On 12 December 2007, Movable Type was relicensed as free software under the GNU General Public License...
by repeatedly placing comments to various blog posts that provided nothing more than a link to the spammer's commercial web site.
Similar attacks
Attack (computer)
In computer and computer networks an attack is any attempt to destroy, expose, alter, disable, steal or gain unauthorized access to or make unauthorized use of an asset.- IETF :Internet Engineering Task Force defines attack in RFC 2828 as:...
are often performed against wiki
Wiki
A wiki is a website that allows the creation and editing of any number of interlinked web pages via a web browser using a simplified markup language or a WYSIWYG text editor. Wikis are typically powered by wiki software and are often used collaboratively by multiple users. Examples include...
s and guestbook
Guestbook
A guestbook is a paper or electronic means for a visitor to acknowledge their visitation to a site, physical or web-based, and leave their name, postal or electronic address , and a comment or note, if desired...
s, both of which accept user contributions.
Spam targeting video sharing sites
Video sharingVideo hosting service
A video hosting service allows individuals to upload video clips to an Internet website. The video host will then store the video on its server, and show the individual different types of code to allow others to view this video...
sites, such as YouTube
YouTube
YouTube is a video-sharing website, created by three former PayPal employees in February 2005, on which users can upload, view and share videos....
, are now being frequently targeted by spammers. The most common technique involves people (or spambots) posting links to sites, most likely pornographic or dealing with online dating, on the comments section of random videos or people's profiles. Another frequently used technique is using bots to post messages on random users' profiles to a spam account's channel page, along with enticing text and images, usually of a sexually suggestive nature. These pages may include their own or other users' videos, again often suggestive. The main purpose of these accounts is to draw people to their link in the home page section of their profile. YouTube has blocked the posting of such links. In addition, YouTube has implemented a CAPTCHA
CAPTCHA
A CAPTCHA is a type of challenge-response test used in computing as an attempt to ensure that the response is generated by a person. The process usually involves one computer asking a user to complete a simple test which the computer is able to generate and grade...
system that makes rapid posting of repeated comments much more difficult than before, because of abuse in the past by mass-spammers who would flood people's profiles with thousands of repetitive comments.
Yet another kind is actual video spam, giving the uploaded movie a name and description with a popular figure or event which is likely to draw attention, or within the video has a certain image timed to come up as the video's thumbnail
Thumbnail
Thumbnails are reduced-size versions of pictures, used to help in recognizing and organizing them, serving the same role for images as a normal text index does for words...
image to mislead the viewer. The actual content of the video ends up being totally unrelated, a Rickroll, sometimes offensive, or just features on-screen text of a link to the site being promoted. Others may upload videos presented in an infomercial
Infomercial
Infomercials are direct response television commercials which generally include a phone number or website. There are long-form infomercials, which are typically between 15 and 30 minutes in length, and short-form infomercials, which are typically 30 seconds to 120 seconds in length. Infomercials...
-like format selling their product which feature actors and paid testimonial
Testimonial
In promotion and of advertising, a testimonial or show consists of a written or spoken statement, sometimes from a person figure, sometimes from a private citizen, extolling the virtue of some product. The term "testimonial" most commonly applies to the sales-pitches attributed to ordinary...
s, though the promoted product or service is of dubious quality and would likely not pass the scrutiny of a standards and practices department at a television station
Television station
A television station is a business, organisation or other such as an amateur television operator that transmits content over terrestrial television. A television transmission can be by analog television signals or, more recently, by digital television. Broadcast television systems standards are...
or cable network
Cable network
A cable channel is a television channel available via cable television. Such channels are usually also available via satellite television, including direct broadcast satellite providers such as DirecTV, Dish Network and BSkyB...
.
SPIT
SPIT (SPam over Internet Telephony)VoIP spam
VoIP spam is unwanted, automatically dialled, pre-recorded phone calls using Voice over Internet Protocol . It is similar to E-mail spam...
is VoIP (Voice over Internet Protocol) spam, usually using SIP (Session Initiation Protocol)
Session Initiation Protocol
The Session Initiation Protocol is an IETF-defined signaling protocol widely used for controlling communication sessions such as voice and video calls over Internet Protocol . The protocol can be used for creating, modifying and terminating two-party or multiparty sessions...
.
Academic Search
Academic Search Engines enable researchers to find academic literature and are used to obtain citation data for calculating performance metrics such as the H-indexH-index
The h-index is an index that attempts to measure both the productivity and impact of the published work of a scientist or scholar. The index is based on the set of the scientist's most cited papers and the number of citations that they have received in other publications...
and impact factor
Impact factor
The impact factor, often abbreviated IF, is a measure reflecting the average number of citations to articles published in science and social science journals. It is frequently used as a proxy for the relative importance of a journal within its field, with journals with higher impact factors deemed...
. Researchers from the University of California, Berkeley
University of California, Berkeley
The University of California, Berkeley , is a teaching and research university established in 1868 and located in Berkeley, California, USA...
and OvGU demonstrated that most (web-based) academic search engines, especially Google Scholar
Google Scholar
Google Scholar is a freely accessible web search engine that indexes the full text of scholarly literature across an array of publishing formats and disciplines. Released in beta in November 2004, the Google Scholar index includes most peer-reviewed online journals of Europe and America's largest...
, are not capable of identifying spam attacks. The researchers manipulated the citation counts of articles, and managed to make Google Scholar index complete fake articles, some containing advertising.
Noncommercial forms
E-mail and other forms of spamming have been used for purposes other than advertisements. Many early Usenet spams were religious or political. Serdar ArgicSerdar Argic
Serdar Argic was the alias used in one of the first automated newsgroup spam incidents on Usenet, with the objective of refuting the Armenian Genocide.-Usenet posts:...
, for instance, spammed Usenet with historical revisionist screeds. A number of evangelists
Evangelism
Evangelism refers to the practice of relaying information about a particular set of beliefs to others who do not hold those beliefs. The term is often used in reference to Christianity....
have spammed Usenet
Usenet
Usenet is a worldwide distributed Internet discussion system. It developed from the general purpose UUCP architecture of the same name.Duke University graduate students Tom Truscott and Jim Ellis conceived the idea in 1979 and it was established in 1980...
and e-mail media with preaching messages. A growing number of criminals are also using spam to perpetrate various sorts of fraud.
Geographical origins
A 2009 Cisco SystemsCisco Systems
Cisco Systems, Inc. is an American multinational corporation headquartered in San Jose, California, United States, that designs and sells consumer electronics, networking, voice, and communications technology and services. Cisco has more than 70,000 employees and annual revenue of US$...
report lists the origin of spam by country as follows:
| Rank | Country | Spam messages per year (in trillions) |
|---|---|---|
| 1 |  Brazil Brazil |
7.7 |
| 2 |  United States United States |
6.6 |
| 3 |  India India |
3.6 |
| 4 |  South Korea South Korea |
3.1 |
| 5 |  Turkey Turkey |
2.6 |
| 6 |  Vietnam Vietnam |
2.5 |
| 7 |  Mainland China Mainland China |
2.4 |
| 8 |  Poland Poland |
2.4 |
| 9 |  Russia Russia |
2.3 |
| 10 |  Argentina Argentina |
1.5 |
Pre-Internet
In the late 19th Century Western UnionWestern Union
The Western Union Company is a financial services and communications company based in the United States. Its North American headquarters is in Englewood, Colorado. Up until 2006, Western Union was the best-known U.S...
allowed telegraphic messages on its network to be sent to multiple destinations. The first recorded instance of a mass unsolicited commercial telegram is from May 1864. Up until the Great Depression
Great Depression
The Great Depression was a severe worldwide economic depression in the decade preceding World War II. The timing of the Great Depression varied across nations, but in most countries it started in about 1929 and lasted until the late 1930s or early 1940s...
wealthy North American residents would be deluged with nebulous investment offers. This problem never fully emerged in Europe to the degree that it did in the Americas, because telegraphy was regulated by national post offices in the European region.
Etymology
According to the Internet SocietyInternet Society
The Internet Society or ISOC is an international, nonprofit organization founded during 1992 to provide direction in Internet related standards, education, and policy...
and other sources, the term spam is derived from the 1970 Spam
Spam (Monty Python)
"Spam" is a popular Monty Python sketch, first televised in 1970. In the sketch, two customers are in a greasy spoon café trying to order a breakfast from a menu that includes the processed meat product in almost every dish. The term spam is derived from this sketch...
sketch
Sketch comedy
A sketch comedy consists of a series of short comedy scenes or vignettes, called "sketches," commonly between one and ten minutes long. Such sketches are performed by a group of comic actors or comedians, either on stage or through an audio and/or visual medium such as broadcasting...
of the BBC
BBC
The British Broadcasting Corporation is a British public service broadcaster. Its headquarters is at Broadcasting House in the City of Westminster, London. It is the largest broadcaster in the world, with about 23,000 staff...
television comedy series Monty Python's Flying Circus
Monty Python's Flying Circus
Monty Python’s Flying Circus is a BBC TV sketch comedy series. The shows were composed of surreality, risqué or innuendo-laden humour, sight gags and observational sketches without punchlines...
. The sketch is set in a cafe
Café
A café , also spelled cafe, in most countries refers to an establishment which focuses on serving coffee, like an American coffeehouse. In the United States, it may refer to an informal restaurant, offering a range of hot meals and made-to-order sandwiches...
where nearly every item on the menu includes Spam
Spam (food)
Spam is a canned precooked meat product made by the Hormel Foods Corporation, first introduced in 1937. The labeled ingredients in the classic variety of Spam are chopped pork shoulder meat, with ham meat added, salt, water, modified potato starch as a binder, and sodium nitrite as a preservative...
canned luncheon meat. As the waiter recites the Spam-filled menu, a chorus of Viking
Viking
The term Viking is customarily used to refer to the Norse explorers, warriors, merchants, and pirates who raided, traded, explored and settled in wide areas of Europe, Asia and the North Atlantic islands from the late 8th to the mid-11th century.These Norsemen used their famed longships to...
patrons drowns out all conversations with a song repeating "Spam, Spam, Spam, Spam... lovely Spam! wonderful Spam!", hence "Spamming" the dialogue. The excessive amount of Spam mentioned in the sketch is a reference to the preponderance of imported canned meat products in the United Kingdom, particularly a brand of spiced ham (SPiced hAM = SPAM) from the USA, in the years after World War II, as the country struggled to rebuild its agricultural base. Spam captured a large slice of the British market within lower economic classes and became a byword among British children of the 1960s for low-grade fodder due to its commonality, monotonous taste and cheap price - hence the humour of the Python sketch.
In the early 1980's, companies that bulk-mailed unsolicited advertising material routinely referred to it as "SPAM" - their acronym for "Sales Promotion and Marketing".
In the 1980s the term was adopted to describe certain abusive users who frequented BBSs
Bulletin board system
A Bulletin Board System, or BBS, is a computer system running software that allows users to connect and log in to the system using a terminal program. Once logged in, a user can perform functions such as uploading and downloading software and data, reading news and bulletins, and exchanging...
and MUD
MUD
A MUD , pronounced , is a multiplayer real-time virtual world, with the term usually referring to text-based instances of these. MUDs combine elements of role-playing games, hack and slash, player versus player, interactive fiction, and online chat...
s, who would repeat "Spam" a huge number of times to scroll other users' text off the screen. In early Chat rooms services like PeopleLink and the early days of Online America (later known as America Online or AOL), they actually flooded the screen with quotes from the Monty Python Spam sketch. With internet connections over phone lines, typically running at 1200 or even 300 bit/s
Bit rate
In telecommunications and computing, bit rate is the number of bits that are conveyed or processed per unit of time....
, it could take an enormous amount of time for a spammy logo, drawn in ASCII art
ASCII art
ASCII art is a graphic design technique that uses computers for presentation and consists of pictures pieced together from the 95 printable characters defined by the ASCII Standard from 1963 and ASCII compliant character sets with proprietary extended characters...
to scroll to completion on a viewer's terminal. Sending an irritating, large, meaningless block of text in this way was called spamming. This was used as a tactic by insiders of a group that wanted to drive newcomers out of the room so the usual conversation could continue. It was also used to prevent members of rival groups from chatting—for instance, Star Wars fans often invaded Star Trek
Star Trek
Star Trek is an American science fiction entertainment franchise created by Gene Roddenberry. The core of Star Trek is its six television series: The Original Series, The Animated Series, The Next Generation, Deep Space Nine, Voyager, and Enterprise...
chat rooms, filling the space with blocks of text until the Star Trek fans left. This act, previously called flooding or trashing, came to be known as spamming. The term was soon applied to a large amount of text broadcast by many users.
It later came to be used on Usenet
Usenet
Usenet is a worldwide distributed Internet discussion system. It developed from the general purpose UUCP architecture of the same name.Duke University graduate students Tom Truscott and Jim Ellis conceived the idea in 1979 and it was established in 1980...
to mean excessive multiple posting—the repeated posting of the same message. The unwanted message would appear in many if not all newsgroups, just as Spam appeared in nearly all the menu items in the Monty Python sketch. The first usage of this sense was by Joel Furr
Joel Furr
Joel K. "Jay" Furr is a writer and software trainer notable as a Usenet personality in the early and mid 1990s....
in the aftermath of the ARMM
ARMM (Usenet)
Automated Retroactive Minimal Moderation was a program developed by Richard Depew in 1993 to aid in the control of Usenet abuse. Concerned by abusive posts emanating from certain anonymous-posting sites, Depew developed ARMM to allow news administrators to automatically issue cancel messages for...
incident of March 31, 1993, in which a piece of experimental software released dozens of recursive messages onto the news.admin.policy newsgroup. This use had also become established—to spam Usenet was flooding newsgroups with junk messages. The word was also attributed to the flood of "Make Money Fast
Make Money Fast
"MAKE.MONEY.FAST" is a title of an electronically forwarded chain letter which became so infamous that the term is now used to describe all sorts of chain letters forwarded over the Internet, by e-mail spam or Usenet newsgroups...
" messages that clogged many newsgroups during the 1990s. In 1998, the New Oxford Dictionary of English, which had previously only defined "spam" in relation to the trademarked food product, added a second definition to its entry for "spam": "Irrelevant or inappropriate messages sent on the Internet to a large number of newsgroups or users."
There are several popular false etymologies
False etymology
Folk etymology is change in a word or phrase over time resulting from the replacement of an unfamiliar form by a more familiar one. Unanalyzable borrowings from foreign languages, like asparagus, or old compounds such as samblind which have lost their iconic motivation are...
of the word "spam". One, promulgated by early spammers Laurence Canter and Martha Siegel, is that "spamming" is what happens when one dumps a can of Spam luncheon meat into a fan blade. Another is the backronym
Backronym
A backronym or bacronym is a phrase constructed purposely, such that an acronym can be formed to a specific desired word. Backronyms may be invented with serious or humorous intent, or may be a type of false or folk etymology....
stupid pointless annoying messages". There was also an effort to differentiate between types of spam. That which was sent indiscriminately to any e-mail address was true spam while that which was targeted to more likely prospects, although just as unsolicited, was called velveeta
Velveeta
Velveeta is the brand name of a processed cheese product having a taste that is identified as a type of American cheese with a texture that is softer and smoother. It was first made in 1918 by Swiss immigrant Emil Frey of the Monroe Cheese Company in Monroe, New York. In 1923, The Velveeta Cheese...
(after the cheese product). But this latter term didn't persist.
History of Internet spam
The earliest documented spam (although the term had not yet been coined) was a message advertising the availability of a new model of Digital Equipment CorporationDigital Equipment Corporation
Digital Equipment Corporation was a major American company in the computer industry and a leading vendor of computer systems, software and peripherals from the 1960s to the 1990s...
computers sent by Gary Thuerk to 393 recipients on ARPANET
ARPANET
The Advanced Research Projects Agency Network , was the world's first operational packet switching network and the core network of a set that came to compose the global Internet...
in 1978. Rather than send a separate message to each person, which was the standard practice at the time, he had an assistant, Carl Gartley, write a single mass e-mail. Reaction from the net community was fiercely negative, but the spam did generate some sales.
Spamming had been practiced as a prank by participants in multi-user dungeon games, to fill their rivals' accounts with unwanted electronic junk. The first known electronic chain letter
Chain letter
A typical chain letter consists of a message that attempts to the recipient to make a number of copies of the letter and then pass them on to as many recipients as possible...
, titled Make Money Fast
Make Money Fast
"MAKE.MONEY.FAST" is a title of an electronically forwarded chain letter which became so infamous that the term is now used to describe all sorts of chain letters forwarded over the Internet, by e-mail spam or Usenet newsgroups...
, was released in 1988.
The first major commercial spam incident started on March 5, 1994, when a husband and wife team of lawyers, Laurence Canter and Martha Siegel, began using bulk Usenet
Usenet
Usenet is a worldwide distributed Internet discussion system. It developed from the general purpose UUCP architecture of the same name.Duke University graduate students Tom Truscott and Jim Ellis conceived the idea in 1979 and it was established in 1980...
posting to advertise immigration
Immigration
Immigration is the act of foreigners passing or coming into a country for the purpose of permanent residence...
law services. The incident was commonly termed the "Green Card
United States Permanent Resident Card
United States lawful permanent residency refers to a person's immigration status: the person is authorized to live and work in the United States of America on a permanent basis....
spam", after the subject line of the postings. Defiant in the face of widespread condemnation, the attorneys claimed their detractors were hypocrites or "zealouts", claimed they had a free speech right to send unwanted commercial messages, and labeled their opponents "anti-commerce radicals." The couple wrote a controversial book entitled How to Make a Fortune on the Information Superhighway.
Within a few years, the focus of spamming (and anti-spam efforts) moved chiefly to e-mail, where it remains today. Arguably, the aggressive email spamming by a number of high-profile spammers such as Sanford Wallace
Sanford Wallace
Sanford "Spamford" Wallace came to notoriety in 1997, promoting himself as the original Spam King. Wallace's prolific spamming has resulted in encounters with the United States government, anti-spam activists, and large corporations such as Facebook and MySpace...
of Cyber Promotions in the mid-to-late 1990s contributed to making spam predominantly an email phenomenon in the public mind. By 2009, the majority of spam sent around the world was in the English language
English language
English is a West Germanic language that arose in the Anglo-Saxon kingdoms of England and spread into what was to become south-east Scotland under the influence of the Anglian medieval kingdom of Northumbria...
; spammers began using automatic translation services to send spam in other languages.
Trademark issues
Hormel Foods Corporation, the maker of SPAMSpam
Spam may refer to:* Spam , a canned pork meat product* Spam , unsolicited or undesired electronic messages* E-mail spam, unsolicited or undesired email messages* "Spam" , a comedy sketch...
luncheon meat, does not object to the Internet use of the term "spamming". However, they did ask that the capitalized word "Spam" be reserved to refer to their product and trademark. By and large, this request is obeyed in forums which discuss spam. In Hormel Foods v SpamArrest, Hormel attempted to assert its trademark rights against SpamArrest, a software company, from using the mark "spam", since Hormel owns the trademark. In a dilution claim, Hormel argued that Spam Arrest's use of the term "spam" had endangered and damaged "substantial goodwill and good reputation" in connection with its trademarked lunch meat and related products. Hormel also asserts that Spam Arrest's name so closely resembles its luncheon meat that the public might become confused, or might think that Hormel endorses Spam Arrest's products.
Hormel did not prevail. Attorney Derek Newman responded on behalf of Spam Arrest: "Spam has become ubiquitous throughout the world to describe unsolicited commercial e-mail. No company can claim trademark rights on a generic term." Hormel stated on its website: "Ultimately, we are trying to avoid the day when the consuming public asks, 'Why would Hormel Foods name its product after junk email?".
Hormel also made two attempts that were dismissed in 2005 to revoke the marks "SPAMBUSTER" and Spam Cube
Spam Cube
Founded in 2002 by Joseph P. Marino and Jonathan Fortin, Spam Cube, Inc is a high-tech startup company based in midtown area of New York City. The company designs and manufactures the Spam Cube, a SaaS network security hardware device for consumers that blocks spam e-mail, computer viruses and...
. Hormel's Corporate Attorney Melanie J. Neumann also sent SpamCop
SpamCop
SpamCop is a free spam reporting service, allowing recipients of unsolicited bulk email and unsolicited commercial email to report offenders to the senders' Internet Service Providers , and sometimes their web hosts...
's Julian Haight a letter on August 27, 1999 requesting that he delete an objectionable image (a can of Hormel's Spam luncheon meat product in a trash can), change references to UCE spam to all lower case letters, and confirm his agreement to do so.
Cost-benefit analyses
The European UnionEuropean Union
The European Union is an economic and political union of 27 independent member states which are located primarily in Europe. The EU traces its origins from the European Coal and Steel Community and the European Economic Community , formed by six countries in 1958...
's Internal Market Commission estimated in 2001 that "junk e-mail" cost Internet users €10 billion per year worldwide. The California legislature found that spam cost United States organizations alone more than $13 billion in 2007, including lost productivity and the additional equipment, software, and manpower needed to combat the problem. Spam's direct effects include the consumption of computer and network resources, and the cost in human time and attention of dismissing unwanted messages. Large companies who are frequent spam targets utilize numerous techniques to detect and prevent spam.
In addition, spam has costs stemming from the kinds of spam messages sent, from the ways spammers send them, and from the arms race
Arms race
The term arms race, in its original usage, describes a competition between two or more parties for the best armed forces. Each party competes to produce larger numbers of weapons, greater armies, or superior military technology in a technological escalation...
between spammers and those who try to stop or control spam. In addition, there are the opportunity cost of those who forgo the use of spam-afflicted systems. There are the direct costs, as well as the indirect costs borne by the victims—both those related to the spamming itself, and to other crimes that usually accompany it, such as financial theft, identity theft
Identity theft
Identity theft is a form of stealing another person's identity in which someone pretends to be someone else by assuming that person's identity, typically in order to access resources or obtain credit and other benefits in that person's name...
, data and intellectual property theft, virus
Computer virus
A computer virus is a computer program that can replicate itself and spread from one computer to another. The term "virus" is also commonly but erroneously used to refer to other types of malware, including but not limited to adware and spyware programs that do not have the reproductive ability...
and other malware
Malware
Malware, short for malicious software, consists of programming that is designed to disrupt or deny operation, gather information that leads to loss of privacy or exploitation, or gain unauthorized access to system resources, or that otherwise exhibits abusive behavior...
infection, child pornography, fraud
Fraud
In criminal law, a fraud is an intentional deception made for personal gain or to damage another individual; the related adjective is fraudulent. The specific legal definition varies by legal jurisdiction. Fraud is a crime, and also a civil law violation...
, and deceptive marketing
False advertising
False advertising or deceptive advertising is the use of false or misleading statements in advertising. As advertising has the potential to persuade people into commercial transactions that they might otherwise avoid, many governments around the world use regulations to control false, deceptive or...
.
The cost to providers of search engines
Web search engine
A web search engine is designed to search for information on the World Wide Web and FTP servers. The search results are generally presented in a list of results often referred to as SERPS, or "search engine results pages". The information may consist of web pages, images, information and other...
is not insignificant: "The secondary consequence of spamming is that search engine indexes are inundated with useless pages, increasing the cost of each processed query". The methods of spammers are likewise costly. Because spamming contravenes the vast majority of ISPs' acceptable-use policies, most spammers have for many years gone to some trouble to conceal the origins of their spam. E-mail, Usenet, and instant-message spam are often sent through insecure proxy server
Proxy server
In computer networks, a proxy server is a server that acts as an intermediary for requests from clients seeking resources from other servers. A client connects to the proxy server, requesting some service, such as a file, connection, web page, or other resource available from a different server...
s belonging to unwilling third parties. Spammers frequently use false names, addresses, phone numbers, and other contact information to set up "disposable" accounts at various Internet service providers. In some cases, they have used falsified or stolen credit card
Credit card
A credit card is a small plastic card issued to users as a system of payment. It allows its holder to buy goods and services based on the holder's promise to pay for these goods and services...
numbers to pay for these accounts. This allows them to quickly move from one account to the next as each one is discovered and shut down by the host ISPs.
The costs of spam also include the collateral costs of the struggle between spammers and the administrators and users of the media threatened by spamming. Many users are bothered by spam because it impinges upon the amount of time they spend reading their e-mail. Many also find the content of spam frequently offensive, in that pornography
Pornography
Pornography or porn is the explicit portrayal of sexual subject matter for the purposes of sexual arousal and erotic satisfaction.Pornography may use any of a variety of media, ranging from books, magazines, postcards, photos, sculpture, drawing, painting, animation, sound recording, film, video,...
is one of the most frequently advertised products. Spammers send their spam largely indiscriminately, so pornographic ads may show up in a work place e-mail inbox—or a child's, the latter of which is illegal in many jurisdictions. Recently, there has been a noticeable increase in spam advertising websites that contain child pornography
Child pornography
Child pornography refers to images or films and, in some cases, writings depicting sexually explicit activities involving a child...
.
Some spammers argue that most of these costs could potentially be alleviated by having spammers reimburse ISPs and persons for their material. There are three problems with this logic: first, the rate of reimbursement they could credibly budget is not nearly high enough to pay the direct costs , second, the human cost (lost mail, lost time, and lost opportunities) is basically unrecoverable, and third, spammers often use stolen bank accounts and credit cards to finance their operations, and would conceivably do so to pay off any fines imposed.
E-mail spam exemplifies a tragedy of the commons
Tragedy of the commons
The tragedy of the commons is a dilemma arising from the situation in which multiple individuals, acting independently and rationally consulting their own self-interest, will ultimately deplete a shared limited resource, even when it is clear that it is not in anyone's long-term interest for this...
: spammers use resources (both physical and human), without bearing the entire cost of those resources. In fact, spammers commonly do not bear the cost at all. This raises the costs for everyone. In some ways spam is even a potential threat
Threat (computer)
In Computer security a threat is a possible danger that might exploit a vulnerability to breach security and thus cause possible harm.A threat can be either "intentional" or "accidental" In Computer security a threat is a possible danger that might exploit a vulnerability to breach security and...
to the entire e-mail system, as operated in the past. Since e-mail is so cheap to send, a tiny number of spammers can saturate the Internet with junk mail. Although only a tiny percentage of their targets are motivated to purchase their products (or fall victim to their scams), the low cost may provide a sufficient conversion rate to keep the spamming alive. Furthermore, even though spam appears not to be economically viable as a way for a reputable company to do business, it suffices for professional spammers to convince a tiny proportion of gullible advertisers that it is viable for those spammers to stay in business. Finally, new spammers go into business every day, and the low costs allow a single spammer to do a lot of harm before finally realizing that the business is not profitable.
Some companies and groups "rank" spammers; spammers who make the news are sometimes referred to by these rankings. The secretive nature of spamming operations makes it difficult to determine how proliferated an individual spammer is, thus making the spammer hard to track, block or avoid. Also, spammers may target different networks to different extents, depending on how successful they are at attacking the target. Thus considerable resources are employed to actually measure the amount of spam generated by a single person or group. For example, victims that use common anti-spam hardware, software or services provide opportunities for such tracking. Nevertheless, such rankings should be taken with a grain of salt.
General costs
In all cases listed above, including both commercial and non-commercial, "spam happens" because of a positive Cost-benefit analysisCost-benefit analysis
Cost–benefit analysis , sometimes called benefit–cost analysis , is a systematic process for calculating and comparing benefits and costs of a project for two purposes: to determine if it is a sound investment , to see how it compares with alternate projects...
result if the cost to recipients is excluded as an externality
Externality
In economics, an externality is a cost or benefit, not transmitted through prices, incurred by a party who did not agree to the action causing the cost or benefit...
the spammer can avoid paying.
Cost is the combination of
- Overhead: The costs and overhead of electronic spamming include bandwidth, developing or acquiring an email/wiki/blog spam tool, taking over or acquiring a host/zombie, etc.
- Transaction costTransaction costIn economics and related disciplines, a transaction cost is a cost incurred in making an economic exchange . For example, most people, when buying or selling a stock, must pay a commission to their broker; that commission is a transaction cost of doing the stock deal...
: The incremental cost of contacting each additional recipient once a method of spamming is constructed, multiplied by the number of recipients. (see CAPTCHACAPTCHAA CAPTCHA is a type of challenge-response test used in computing as an attempt to ensure that the response is generated by a person. The process usually involves one computer asking a user to complete a simple test which the computer is able to generate and grade...
as a method of increasing transaction costs) - Risks: Chance and severity of legal and/or public reactions, including damagesDamagesIn law, damages is an award, typically of money, to be paid to a person as compensation for loss or injury; grammatically, it is a singular noun, not plural.- Compensatory damages :...
and punitive damagesPunitive damagesPunitive damages or exemplary damages are damages intended to reform or deter the defendant and others from engaging in conduct similar to that which formed the basis of the lawsuit... - Damage: Impact on the community and/or communication channels being spammed (see Newsgroup spamNewsgroup spamNewsgroup spam is a type of spam where the targets are Usenet newsgroups.Spamming of Usenet newsgroups actually pre-dates e-mail spam. The first widely recognized Usenet spam was posted on 18 January 1994 by Clarence L. Thomas IV, a sysadmin at Andrews University...
)
Benefit is the total expected profit from spam, which may include any combination of the commercial and non-commercial reasons listed above. It is normally linear, based on the incremental benefit of reaching each additional spam recipient, combined with the conversion rate
Conversion rate
In internet marketing, conversion rate is the ratio of visitors who convert casual content views or website visits into desired actions based on subtle or direct requests from marketers, advertisers, and content creators...
. The conversion rate for botnet
Botnet
A botnet is a collection of compromised computers connected to the Internet. Termed "bots," they are generally used for malicious purposes. When a computer becomes compromised, it becomes a part of a botnet...
-generated spam has recently been measured to be around one in 12,000,000 for pharmaceutical spam and one in 200,000 for infection sites as used by the Storm botnet
Storm botnet
The Storm botnet or Storm worm botnet is a remotely controlled network of "zombie" computers that have been linked by the Storm Worm, a Trojan horse spread through e-mail spam...
.
They specifically say in the paper "After 26 days, and almost 350 million e-mail messages, only 28 sales resulted".
Spam is prevalent on the Internet because the transaction cost of electronic communications is radically less than any alternate form of communication, far outweighing the current potential losses, as seen by the amount of spam currently in existence. Spam continues to spread to new forms of electronic communication as the gain (number of potential recipients) increases to levels where the cost/benefit becomes positive. Spam has most recently evolved to include wikispam and blogspam as the levels of readership increase to levels where the overhead is no longer the dominating factor. According to the above analysis, spam levels will continue to increase until the cost/benefit analysis is balanced.
In crime
Spam can be used to spread computer virusComputer virus
A computer virus is a computer program that can replicate itself and spread from one computer to another. The term "virus" is also commonly but erroneously used to refer to other types of malware, including but not limited to adware and spyware programs that do not have the reproductive ability...
es, trojan horses
Trojan horse (computing)
A Trojan horse, or Trojan, is software that appears to perform a desirable function for the user prior to run or install, but steals information or harms the system. The term is derived from the Trojan Horse story in Greek mythology.-Malware:A destructive program that masquerades as a benign...
or other malicious software. The objective may be identity theft
Identity theft
Identity theft is a form of stealing another person's identity in which someone pretends to be someone else by assuming that person's identity, typically in order to access resources or obtain credit and other benefits in that person's name...
, or worse (e.g., advance fee fraud
Advance fee fraud
An advance-fee fraud is a confidence trick in which the target is persuaded to advance sums of money in the hope of realizing a significantly larger gain...
). Some spam attempts to capitalize on human greed whilst other attempts to use the victims' inexperience with computer technology to trick them (e.g., phishing
Phishing
Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT...
). On May 31, 2007, one of the world's most prolific spammers, Robert Alan Soloway, was arrested by U.S. authorities. Described as one of the top ten spammers in the world, Soloway was charged with 35 criminal counts, including mail fraud, wire fraud, e-mail fraud
E-mail fraud
Email fraud is the intentional deception made for personal gain or to damage another individual through email. Almost as soon as email became widely used, it began to be used as a means to defraud people. Email fraud can take the form of a "con game" or scam...
, aggravated identity theft and money laundering. Prosecutors allege that Soloway used millions of "zombie" computers
Zombie computer
In computer science, a zombie is a computer connected to the Internet that has been compromised by a cracker, computer virus or trojan horse and can be used to perform malicious tasks of one sort or another under remote direction. Botnets of zombie computers are often used to spread e-mail spam...
to distribute spam during 2003. This is the first case in which U.S. prosecutors used identity theft laws to prosecute a spammer for taking over someone else's Internet domain name.
In an attempt to assess potential legal and technical strategies for stopping illegal spam, a study from the University of California, San Diego, and the University of California, Berkeley, “Click Trajectories: End-to-End Analysis of the Spam Value Chain” (PDF), cataloged three months of online spam data and researched website naming and hosting infrastructures. The study concluded that: 1) half of all spam programs have their domains and servers distributed over just 8% or fewer of the total available hosting registrars and Autonomous Systems. Overall, 80% of spam programs are distributed over just 20% of all registrars and Autonomous Systems; 2) of the 76 purchases for which the researchers received transaction information, there were only 13 distinct banks acting as credit card acquirers and only three banks provided the payment servicing for 95% of the spam-advertised goods in the study; and, 3) a “financial blacklist” of banking entities that do business with spammers would dramatically reduce monetization of unwanted emails. Moreover, this blacklist could be updated far more rapidly than spammers could acquire new banking resources, an asymmetry favoring anti-spam efforts.
Political issues
Spamming remains a hot discussion topic. In 2004, the seized PorschePorsche
Porsche Automobil Holding SE, usually shortened to Porsche SE a Societas Europaea or European Public Company, is a German based holding company with investments in the automotive industry....
of an indicted spammer was advertised on the Internet; this revealed the extent of the financial rewards available to those who are willing to commit duplicitous acts online. However, some of the possible means used to stop spamming may lead to other side effects, such as increased government control over the Internet, loss of privacy, barriers to free expression, and the commercialization of e-mail.
One of the chief values favored by many long-time Internet users and experts, as well as by many members of the public, is the free exchange of ideas. Many have valued the relative anarchy of the Internet, and bridle at the idea of restrictions placed upon it. A common refrain from spam-fighters is that spamming itself abridges the historical freedom of the Internet, by attempting to force users to carry the costs of material which they would not choose.
An ongoing concern expressed by parties such as the Electronic Frontier Foundation
Electronic Frontier Foundation
The Electronic Frontier Foundation is an international non-profit digital rights advocacy and legal organization based in the United States...
and the American Civil Liberties Union
American Civil Liberties Union
The American Civil Liberties Union is a U.S. non-profit organization whose stated mission is "to defend and preserve the individual rights and liberties guaranteed to every person in this country by the Constitution and laws of the United States." It works through litigation, legislation, and...
has to do with so-called "stealth blocking", a term for ISPs employing aggressive spam blocking without their users' knowledge. These groups' concern is that ISPs or technicians seeking to reduce spam-related costs may select tools which (either through error or design) also block non-spam e-mail from sites seen as "spam-friendly". Spam Prevention Early Warning System
Spam Prevention Early Warning System
The Spam Prevention Early Warning System was an anonymous service which maintained a list of IP address ranges belonging to Internet service providers which host spammers and show little action to prevent their abuse of other networks' resources...
(SPEWS) is a common target of these criticisms. Few object to the existence of these tools; it is their use in filtering the mail of users who are not informed of their use which draws fire.
Some see spam-blocking tools as a threat to free expression—and laws against spamming as an untoward precedent for regulation or taxation of e-mail and the Internet at large. Even though it is possible in some jurisdictions to treat some spam as unlawful merely by applying existing laws against trespass
Trespass
Trespass is an area of tort law broadly divided into three groups: trespass to the person, trespass to chattels and trespass to land.Trespass to the person, historically involved six separate trespasses: threats, assault, battery, wounding, mayhem, and maiming...
and conversion
Conversion (law)
Conversion is a common law tort. A conversion is a voluntary act by one person inconsistent with the ownership rights of another. It is a tort of strict liability...
, some laws specifically targeting spam have been proposed. In 2004, United States passed the CAN-SPAM Act of 2003
CAN-SPAM Act of 2003
The CAN-SPAM Act of 2003 , signed into law by President George W. Bush on December 16, 2003, establishes the United States' first national standards for the sending of commercial e-mail and requires the Federal Trade Commission to enforce its provisions...
which provided ISPs with tools to combat spam. This act allowed Yahoo!
Yahoo!
Yahoo! Inc. is an American multinational internet corporation headquartered in Sunnyvale, California, United States. The company is perhaps best known for its web portal, search engine , Yahoo! Directory, Yahoo! Mail, Yahoo! News, Yahoo! Groups, Yahoo! Answers, advertising, online mapping ,...
to successfully sue Eric Head, reportedly one of the biggest spammers in the world, who settled the lawsuit for several thousand U.S. dollars in June 2004. But the law is criticized by many for not being effective enough. Indeed, the law was supported by some spammers and organizations which support spamming, and opposed by many in the anti-spam community. Examples of effective anti-abuse laws that respect free speech rights include those in the U.S. against unsolicited faxes and phone calls, and those in Australia and a few U.S. states against spam.
In November 2004, Lycos Europe
Lycos Europe
Lycos Europe was a pan-European network of websites, offering services including communication tools, online communities, web search, e-commerce, web hosting, homepage building and Internet access. It was an independent corporation, sharing no corporate structure with Lycos, Inc...
released a screen saver called make LOVE not SPAM which made Distributed Denial of Service attacks
Attack (computer)
In computer and computer networks an attack is any attempt to destroy, expose, alter, disable, steal or gain unauthorized access to or make unauthorized use of an asset.- IETF :Internet Engineering Task Force defines attack in RFC 2828 as:...
on the spammers themselves. It met with a large amount of controversy and the initiative ended in December 2004.
Anti-spam policies may also be a form of disguised censorship, a way to ban access or reference to questioning alternative forums or blogs by an institution. This form of occult censorship is mainly used by private companies when they can not muzzle criticism by legal ways.
United States
Sanford WallaceSanford Wallace
Sanford "Spamford" Wallace came to notoriety in 1997, promoting himself as the original Spam King. Wallace's prolific spamming has resulted in encounters with the United States government, anti-spam activists, and large corporations such as Facebook and MySpace...
and Cyber Promotions were the target of a string of lawsuits, many of which were settled out of court, up through the famous 1998 Earthlink settlement which put Cyber Promotions out of business. Attorney Laurence Canter was disbarred by the Tennessee Supreme Court
Tennessee Supreme Court
The Tennessee Supreme Court is the state supreme court of the state of Tennessee. Cornelia Clark is the current Chief Justice.Unlike other states, in which the state attorney general is directly elected or appointed by the governor or state legislature, the Tennessee Supreme Court appoints the...
in 1997 for sending prodigious amounts of spam advertising his immigration law
Immigration law
Immigration law refers to national government policies which control the phenomenon of immigration to their country.Immigraton law, regarding foreign citizens, is related to nationality law, which governs the legal status of people, in matters such as citizenship...
practice. In 2005, Jason Smathers
Jason Smathers
Jason Smathers is a former employee of America Online.In February 2005, Smathers pled guilty to violations of the US CAN-SPAM Act of 2003. Smathers was accused and convicted of illegally selling approximately 92 million AOL member screen names, belonging to 30 million AOL customers, to a third...
, a former America Online employee, pled guilty to charges of violating the CAN-SPAM Act
CAN-SPAM Act of 2003
The CAN-SPAM Act of 2003 , signed into law by President George W. Bush on December 16, 2003, establishes the United States' first national standards for the sending of commercial e-mail and requires the Federal Trade Commission to enforce its provisions...
. In 2003, he sold a list of approximately 93 million AOL subscriber e-mail addresses to Sean Dunaway who, in turn, sold the list to spammers.
In 2007, Robert Soloway
Robert Soloway
Robert Alan Soloway is the founder of the so-called "Strategic Partnership Against Microsoft Illegal Spam," or SPAMIS, but is said to be one of the Internet's biggest spammers through his company, Newport Internet Marketing . He was arrested on May 30, 2007, after a grand jury indicted him on...
lost a case in a federal court against the operator of a small Oklahoma-based Internet service provider who accused him of spamming. U.S. Judge Ralph G. Thompson granted a motion by plaintiff Robert Braver for a default judgment
Default judgment
Default judgment is a binding judgment in favor of either party based on some failure to take action by the other party. Most often, it is a judgment in favor of a plaintiff when the defendant has not responded to a summons or has failed to appear before a court of law...
and permanent injunction
Injunction
An injunction is an equitable remedy in the form of a court order that requires a party to do or refrain from doing certain acts. A party that fails to comply with an injunction faces criminal or civil penalties and may have to pay damages or accept sanctions...
against him. The judgment includes a statutory damages award of $10,075,000 under Oklahoma law.
In June 2007, two men were convicted of eight counts stemming from sending millions of e-mail spam messages that included hardcore pornographic images. Jeffrey A. Kilbride, 41, of Venice, California was sentenced to six years in prison, and James R. Schaffer, 41, of Paradise Valley, Arizona
Paradise Valley, Arizona
Paradise Valley is a small, affluent town in Maricopa County, Arizona, United States. According to the 2005 Census Bureau, the population of the town was 14,558. Despite the town's relatively small area and population compared to other municipalities in the Phoenix metropolitan area, Paradise...
, was sentenced to 63 months. In addition, the two were fined $100,000, ordered to pay $77,500 in restitution to AOL
AOL
AOL Inc. is an American global Internet services and media company. AOL is headquartered at 770 Broadway in New York. Founded in 1983 as Control Video Corporation, it has franchised its services to companies in several nations around the world or set up international versions of its services...
, and ordered to forfeit more than $1.1 million, the amount of illegal proceeds from their spamming operation. The charges included conspiracy
Conspiracy (crime)
In the criminal law, a conspiracy is an agreement between two or more persons to break the law at some time in the future, and, in some cases, with at least one overt act in furtherance of that agreement...
, fraud
Fraud
In criminal law, a fraud is an intentional deception made for personal gain or to damage another individual; the related adjective is fraudulent. The specific legal definition varies by legal jurisdiction. Fraud is a crime, and also a civil law violation...
, money laundering
Money laundering
Money laundering is the process of disguising illegal sources of money so that it looks like it came from legal sources. The methods by which money may be laundered are varied and can range in sophistication. Many regulatory and governmental authorities quote estimates each year for the amount...
, and transportation of obscene
Obscenity
An obscenity is any statement or act which strongly offends the prevalent morality of the time, is a profanity, or is otherwise taboo, indecent, abhorrent, or disgusting, or is especially inauspicious...
materials. The trial, which began on June 5, was the first to include charges under the CAN-SPAM Act of 2003
CAN-SPAM Act of 2003
The CAN-SPAM Act of 2003 , signed into law by President George W. Bush on December 16, 2003, establishes the United States' first national standards for the sending of commercial e-mail and requires the Federal Trade Commission to enforce its provisions...
, according to a release from the Department of Justice
United States Department of Justice
The United States Department of Justice , is the United States federal executive department responsible for the enforcement of the law and administration of justice, equivalent to the justice or interior ministries of other countries.The Department is led by the Attorney General, who is nominated...
. The specific law that prosecutors used under the CAN-Spam Act was designed to crack down on the transmission of pornography in spam.
In 2005, Scott J. Filary and Donald E. Townsend of Tampa, Florida
Tampa, Florida
Tampa is a city in the U.S. state of Florida. It serves as the county seat for Hillsborough County. Tampa is located on the west coast of Florida. The population of Tampa in 2010 was 335,709....
were sued by Florida Attorney General
Florida Attorney General
The Florida Attorney General is an elected cabinet official in the U.S. state of Florida. The attorney general serves as the chief legal officer of the state....
Charlie Crist
Charlie Crist
Charles Joseph "Charlie" Crist, Jr. is an American politician who was the 44th Governor of Florida. Prior to his election as governor, Crist previously served as Florida State Senator, Education Commissioner, and Attorney General...
for violating the Florida Electronic Mail Communications Act. The two spammers were required to pay $50,000 USD to cover the costs of investigation by the state of Florida
Florida
Florida is a state in the southeastern United States, located on the nation's Atlantic and Gulf coasts. It is bordered to the west by the Gulf of Mexico, to the north by Alabama and Georgia and to the east by the Atlantic Ocean. With a population of 18,801,310 as measured by the 2010 census, it...
, and a $1.1 million penalty if spamming were to continue, the $50,000 was not paid, or the financial statements provided were found to be inaccurate. The spamming operation was successfully shut down.
Edna Fiedler, 44, of Olympia, Washington
Olympia, Washington
Olympia is the capital city of the U.S. state of Washington and the county seat of Thurston County. It was incorporated on January 28, 1859. The population was 46,478 at the 2010 census...
, on June 25, 2008, pleaded guilty in a Tacoma court and was sentenced to 2 years imprisonment and 5 years of supervised release or probation
Probation
Probation literally means testing of behaviour or abilities. In a legal sense, an offender on probation is ordered to follow certain conditions set forth by the court, often under the supervision of a probation officer...
in an Internet $1 million "Nigerian check scam." She conspired to commit bank, wire and mail fraud, against US citizens, specifically using Internet by having had an accomplice
Accomplice
At law, an accomplice is a person who actively participates in the commission of a crime, even though they take no part in the actual criminal offense. For example, in a bank robbery, the person who points the gun at the teller and asks for the money is guilty of armed robbery...
who shipped counterfeit checks and money orders to her from Lagos
Lagos
Lagos is a port and the most populous conurbation in Nigeria. With a population of 7,937,932, it is currently the third most populous city in Africa after Cairo and Kinshasa, and currently estimated to be the second fastest growing city in Africa...
, Nigeria, last November. Fiedler shipped out $ 609,000 fake check and money orders when arrested and prepared to send additional $ 1.1 million counterfeit materials. Also, the U.S. Postal Service recently intercepted counterfeit checks, lottery tickets and eBay overpayment schemes with a face value of $2.1 billion.
United Kingdom
In the first successful case of its kind, Nigel Roberts from the Channel IslandsChannel Islands
The Channel Islands are an archipelago of British Crown Dependencies in the English Channel, off the French coast of Normandy. They include two separate bailiwicks: the Bailiwick of Guernsey and the Bailiwick of Jersey...
won £270 against Media Logistics UK who sent junk e-mails to his personal account.
In January 2007, a Sheriff Court in Scotland awarded Mr. Gordon Dick £750 (the then maximum sum which could be awarded in a Small Claim action) plus expenses of £618.66, a total of £1368.66 against Transcom Internet Services Ltd. for breaching anti-spam laws. Transcom had been legally represented at earlier hearings but were not represented at the proof, so Gordon Dick got his decree by default. It is the largest amount awarded in compensation in the United Kingdom since Roberts -v- Media Logistics case in 2005 above, but it is not known if Mr. Dick ever received anything. (An image of Media Logistics' cheque is shown on Roberts' website
) Both Roberts and Dick are well known figures in the British Internet industry for other things. Dick is currently Interim Chairman of Nominet UK (the manager of .UK and .CO.UK) while Roberts is CEO of CHANNELISLES.NET (manager of .GG and .JE).
Despite the statutory tort that is created by the Regulations implementing the EC Directive, few other people have followed their example. As the Courts engage in active case management, such cases would probably now be expected to be settled by mediation and payment of nominal damages.
New Zealand
In October 2008, a vast international internet spam operation run from New Zealand was cited by American authorities as one of the world’s largest, and for a time responsible for up to a third of all unwanted emails. In a statement the US Federal Trade Commission (FTC) named Christchurch’s Lance Atkinson as one of the principals of the operation. New Zealand’s Internal Affairs announced it had lodged a $200,000 claim in the High Court against Atkinson and his brother Shane AtkinsonShane Atkinson
Shane Atkinson, of Christchurch, New Zealand was a major spammer whose details were leaked on to the Internet soon after an article was written about him in the New Zealand Herald...
and courier Roland Smits, after raids in Christchurch. This marked the first prosecution since the Unsolicited Electronic Messages Act (UEMA) was passed in September 2007.
The FTC said it had received more than three million complaints about spam messages connected to this operation, and estimated that it may be responsible for sending billions of illegal spam messages. The US District Court froze the defendants’ assets to preserve them for consumer redress pending trial.
U.S. co-defendant Jody Smith forfeited more than $800,000 and faces up to five years in prison for charges to which he pled guilty.
Bulgaria
While most countries either outlaw or at least ignore spam, BulgariaBulgaria
Bulgaria , officially the Republic of Bulgaria , is a parliamentary democracy within a unitary constitutional republic in Southeast Europe. The country borders Romania to the north, Serbia and Macedonia to the west, Greece and Turkey to the south, as well as the Black Sea to the east...
is the first and until now only one to legalize it. According to the Bulgarian E-Commerce act (Чл.5,6) anyone can send spam to mailboxes published as owned by a company or organization, as long as there is a "clear and straight indication that the message is unsolicited commercial email" ("да осигури ясното и недвусмислено разпознаване на търговското съобщение като непоискано") in the message body.
This made lawsuits against Bulgarian ISP's and public e-mail providers with antispam policy possible, as they are obstructing legal commerce activity and thus violate Bulgarian antitrust acts. While there are no such lawsuits until now, several cases of spam obstruction are currently awaiting decision in the Bulgarian Antitrust Commission (Комисия за защита на конкуренцията) and can end with serious fines for the ISP's in question.
The law contains other dubious provisions - for example, the creation of a nationwide public electronic register of email addresses that do not want to receive spam. It is usually abused as the perfect source for e-mail address harvesting
E-mail address harvesting
Email harvesting is the process of obtaining lists of email addresses using various methods for use in bulk email or other purposes usually grouped as spam.-Methods:...
, because publishing invalid or incorrect information in such a register is a criminal offense in Bulgaria.
See also
- Address mungingAddress mungingAddress munging is the practice of disguising, or munging, an e-mail address to prevent it being automatically collected and used as a target for people and organizations who send unsolicited bulk e-mail...
(avoidance technique) - Advance fee fraudAdvance fee fraudAn advance-fee fraud is a confidence trick in which the target is persuaded to advance sums of money in the hope of realizing a significantly larger gain...
(Nigerian spam) - Anti-spam techniques
- Bacn
- E-mail fraudE-mail fraudEmail fraud is the intentional deception made for personal gain or to damage another individual through email. Almost as soon as email became widely used, it began to be used as a means to defraud people. Email fraud can take the form of a "con game" or scam...
- Identity theftIdentity theftIdentity theft is a form of stealing another person's identity in which someone pretends to be someone else by assuming that person's identity, typically in order to access resources or obtain credit and other benefits in that person's name...
- Image spamImage spamImage spam is a kind of E-mail spam where the message text of the spam is presented as a picture in an image file. When introduced by spammers most graphical E-mail client software would render the image file by default, presenting the message image directly to the user, it was a highly effective...
- Internet Troll
- Job scams
- Junk mail
- Junk Mail PublishingJunk Mail PublishingJunk Mail Publishing is South Africa's leading publisher in the Classified advertising industry, publishing various products through different Media such as print, World Wide Web, Mobile Web, SMS, and Phone.-History of the company:...
- List of spammers
- Suppression listSuppression listA Suppression List is a list of suppressed e-mail addresses used by e-mail senders to comply with the CAN-SPAM Act of 2003. CAN-SPAM requires that senders of commercial emails provide a functioning opt-out mechanism by which email recipients can unsubscribe their email address from future email...
- MalwareMalwareMalware, short for malicious software, consists of programming that is designed to disrupt or deny operation, gather information that leads to loss of privacy or exploitation, or gain unauthorized access to system resources, or that otherwise exhibits abusive behavior...
- Network Abuse ClearinghouseNetwork Abuse ClearinghouseThe Network Abuse Clearinghouse, better known as abuse.net, maintains a contact database for reporting misuse on the Internet. It makes entries from the database available , and provides an intermediary service for registered users to forward complaints by e-mail.-See also:* Anti-spam techniques *...
- PhishingPhishingPhishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT...
- Scam
- Scad (scam ad)Scad (scam ad)A scad is a portmanteau of the words scam and advertisement, usually in reference to internet spam. The term has been used by the Alliance Against Bait and Click to describe scam ads that lure consumers to click on their site using a brand name or an outrageous deal while in turn providing suspect...
- Social networking spamSocial networking spamSocial networking spam is spam directed at users of internet social networking services such as MySpace, Facebook or LinkedIn. Users of social networking services can send notes, that may include embedded links to other social network locations or even outside sites, to one another.This is where...
- SORBSSorbsSorbs are a Western Slavic people of Central Europe living predominantly in Lusatia, a region on the territory of Germany and Poland. In Germany they live in the states of Brandenburg and Saxony. They speak the Sorbian languages - closely related to Polish and Czech - officially recognized and...
- SpamSpamSpam may refer to:* Spam , a canned pork meat product* Spam , unsolicited or undesired electronic messages* E-mail spam, unsolicited or undesired email messages* "Spam" , a comedy sketch...
- Spam LitSpam LitSpam Lit is defined as snippets of nonsensical verse and prose embedded in spam e-mail messages...
- SpamCopSpamCopSpamCop is a free spam reporting service, allowing recipients of unsolicited bulk email and unsolicited commercial email to report offenders to the senders' Internet Service Providers , and sometimes their web hosts...
- Spamhaus
- SpamigationSpamigationSpamigation is mass litigation conducted to intimidate large numbers of people. The term was coined by Brad Templeton of the Electronic Frontier Foundation to explain the tactics of the Recording Industry Association of America , which files large numbers of lawsuits against individuals for file...
- SPIT (SPam over Internet Telephony)VoIP spamVoIP spam is unwanted, automatically dialled, pre-recorded phone calls using Voice over Internet Protocol . It is similar to E-mail spam...
- SpoetrySpoetrySpoetry or spoems are poetic verses made primarily from the subject lines of spam e-mail messages.-What is spoetry?:It is unknown as to when the first spoem was started as several writers and bloggers have claimed to have created the form. However, it is estimated that the idea began in 1999 as...
- SporgerySporgerySporgery is the disruptive act of posting a flood of articles to a Usenet newsgroup, with the article headers falsified so that they appear to have been posted by others. The word is a portmanteau of spam and forgery, coined by German software developer and critic of Scientology Tilman...
- Virus (computer)
- VishingVishingVishing is the criminal practice of using social engineering over the telephone system, most often using features facilitated by Voice over IP , to gain access to private personal and financial information from the public for the purpose of financial reward. The term is a combination of "voice" and...
History
- Howard CarmackHoward CarmackHoward Carmack was the first spammer, i.e. notorious sender of spam e-mails, to be sentenced to a time in jail.He was arrested in May 2003 and first freed for a bail of $20,000....
- Make money fastMake Money Fast"MAKE.MONEY.FAST" is a title of an electronically forwarded chain letter which became so infamous that the term is now used to describe all sorts of chain letters forwarded over the Internet, by e-mail spam or Usenet newsgroups...
- Sanford WallaceSanford WallaceSanford "Spamford" Wallace came to notoriety in 1997, promoting himself as the original Spam King. Wallace's prolific spamming has resulted in encounters with the United States government, anti-spam activists, and large corporations such as Facebook and MySpace...
- Spam KingSpam KingThe title Spam King may refer to:* Eddie Davidson , American spammer, 2002–2007* Oleg Nikolaenko , Russian spammer waiting US federal trial* Alan Ralsky , American fraudster who gained notoriety after a 2002 Slashdot posting...
- Usenet Death PenaltyUsenet Death PenaltyOn Usenet, the Usenet Death Penalty is a final penalty that may be issued against Internet service providers or single users who produce too much spam or fail to adhere to Usenet standards...
- UUnetUUNETUUNET founded in 1987, was one of the largest Internet service providers and one of the nine Tier 1 networks. It was based in Northern Virginia and was the first commercial Internet service provider...
Further reading
- Sjouwerman, Stu; Posluns, Jeffrey, "Inside the spam cartel: trade secrets from the dark side", Elsevier/Syngress; 1st edition, November 27, 2004. ISBN 978-1-932266-86-3
External links
- Spamtrackers SpamWiki: a peer-reviewed spam information and analysis resource.
- Federal Trade Commission page advising people to forward spam e-mail to them
- Slamming Spamming Resource on Spam
- Why am I getting all this spam? CDT
- Cybertelecom:: Federal spam law and policy
- Reaction to the DEC Spam of 1978 Overview and text of the first known internet email spam.
- Malware City - The Spam Omelette BitDefender’s weekly report on spam trends and techniques.
- 1 December 2009: arrest of a major spammer
- EatSpam.org - This website provides you with disposable e-mail addresses which expire after 15 Minutes. You can read and reply to e-mails that are sent to the temporary e-mail address within the given time frame.
- Spam Analysis of 2010 and estimated Spam for 2011 - Article about Spam Analysis of 2010 and estimated Spam for 2011

