
Enigma machine
Encyclopedia


Electromechanics
In engineering, electromechanics combines the sciences of electromagnetism, of electrical engineering and mechanics. Mechanical engineering in this context refers to the larger discipline which includes chemical engineering, and other related disciplines. Electrical engineering in this context...
rotor cipher machines
Rotor machine
In cryptography, a rotor machine is an electro-mechanical device used for encrypting and decrypting secret messages. Rotor machines were the cryptographic state-of-the-art for a prominent period of history; they were in widespread use in the 1920s–1970s...
used for the encryption
Encryption
In cryptography, encryption is the process of transforming information using an algorithm to make it unreadable to anyone except those possessing special knowledge, usually referred to as a key. The result of the process is encrypted information...
and decryption of secret messages. Enigma was invented by German
Germans
The Germans are a Germanic ethnic group native to Central Europe. The English term Germans has referred to the German-speaking population of the Holy Roman Empire since the Late Middle Ages....
engineer Arthur Scherbius
Arthur Scherbius
Arthur Scherbius was a German electrical engineer who patented an invention for a mechanical cipher machine, later sold as the Enigma machine.Scherbius was born in Frankfurt am Main and his father was a small businessman...
at the end of World War I
World War I
World War I , which was predominantly called the World War or the Great War from its occurrence until 1939, and the First World War or World War I thereafter, was a major war centred in Europe that began on 28 July 1914 and lasted until 11 November 1918...
. The early models were used commercially from the early 1920s, and adopted by military and government services of several countries — most notably by Nazi Germany
Nazi Germany
Nazi Germany , also known as the Third Reich , but officially called German Reich from 1933 to 1943 and Greater German Reich from 26 June 1943 onward, is the name commonly used to refer to the state of Germany from 1933 to 1945, when it was a totalitarian dictatorship ruled by...
before and during World War II
World War II
World War II, or the Second World War , was a global conflict lasting from 1939 to 1945, involving most of the world's nations—including all of the great powers—eventually forming two opposing military alliances: the Allies and the Axis...
. Several different Enigma models were produced, but the German military
Wehrmacht
The Wehrmacht – from , to defend and , the might/power) were the unified armed forces of Nazi Germany from 1935 to 1945. It consisted of the Heer , the Kriegsmarine and the Luftwaffe .-Origin and use of the term:...
models are the ones most commonly discussed.
In December 1932, the Polish Cipher Bureau first broke Germany's military Enigma ciphers. Five weeks before the outbreak of World War II, on 25 July 1939, in Warsaw, they presented their Enigma-decryption techniques
Cryptanalysis of the Enigma
Cryptanalysis of the Enigma enabled the western Allies in World War II to read substantial amounts of secret Morse-coded radio communications of the Axis powers that had been enciphered using Enigma machines. This yielded military intelligence which, along with that from other decrypted Axis radio...
and equipment to French and British military intelligence
Military intelligence
Military intelligence is a military discipline that exploits a number of information collection and analysis approaches to provide guidance and direction to commanders in support of their decisions....
. Thanks to this, during the war, Allied
Allies of World War II
The Allies of World War II were the countries that opposed the Axis powers during the Second World War . Former Axis states contributing to the Allied victory are not considered Allied states...
codebreakers
Cryptanalysis
Cryptanalysis is the study of methods for obtaining the meaning of encrypted information, without access to the secret information that is normally required to do so. Typically, this involves knowing how the system works and finding a secret key...
were able to decrypt a vast number of messages that had been enciphered using the Enigma. The intelligence
Military intelligence
Military intelligence is a military discipline that exploits a number of information collection and analysis approaches to provide guidance and direction to commanders in support of their decisions....
gleaned from this source, codenamed "Ultra
Ultra
Ultra was the designation adopted by British military intelligence in June 1941 for wartime signals intelligence obtained by "breaking" high-level encrypted enemy radio and teleprinter communications at the Government Code and Cypher School at Bletchley Park. "Ultra" eventually became the standard...
" by the British, was a substantial aid to the Allied war effort.
The exact influence of Ultra on the course of the war is debated; an oft-repeated assessment is that decryption of German ciphers hastened the end of the European war
Victory in Europe Day
Victory in Europe Day commemorates 8 May 1945 , the date when the World War II Allies formally accepted the unconditional surrender of the armed forces of Nazi Germany and the end of Adolf Hitler's Third Reich. The formal surrender of the occupying German forces in the Channel Islands was not...
by two years. Winston Churchill
Winston Churchill
Sir Winston Leonard Spencer-Churchill, was a predominantly Conservative British politician and statesman known for his leadership of the United Kingdom during the Second World War. He is widely regarded as one of the greatest wartime leaders of the century and served as Prime Minister twice...
told Britain's King George VI after World War II: "It was thanks to Ultra that we won the war."
Although Enigma had some cryptographic weaknesses, in practice it was only in combination with procedural flaws, operator mistakes, captured key tables and hardware, that Allied cryptanalysts were able to be so successful.
Description
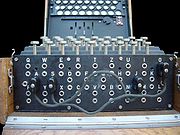
Like other rotor machines, the Enigma machine is a combination of mechanical and electrical subsystems. The mechanical subsystem consists of a keyboard; a set of rotating disks called rotors arranged adjacently along a spindleAxle
An axle is a central shaft for a rotating wheel or gear. On wheeled vehicles, the axle may be fixed to the wheels, rotating with them, or fixed to its surroundings, with the wheels rotating around the axle. In the former case, bearings or bushings are provided at the mounting points where the axle...
; and one of various stepping components to turn one or more of the rotors with each key press.
Electrical pathway

Electrical network
An electrical network is an interconnection of electrical elements such as resistors, inductors, capacitors, transmission lines, voltage sources, current sources and switches. An electrical circuit is a special type of network, one that has a closed loop giving a return path for the current...
. When a key is pressed, a circuit is completed with current flowing through the various components in their current configuration and ultimately lighting one of the display lamps
Lamp (electrical component)
A lamp is a replaceable component such as an incandescent light bulb, which is designed to produce light from electricity. These components usually have a base of ceramic, metal, glass or plastic, which makes an electrical connection in the socket of a light fixture. This connection may be made...
, indicating the output letter. For example, when encrypting a message starting ANX…, the operator would first press the A key, and the Z lamp might light, so Z would be the first letter of the ciphertext
Ciphertext
In cryptography, ciphertext is the result of encryption performed on plaintext using an algorithm, called a cipher. Ciphertext is also known as encrypted or encoded information because it contains a form of the original plaintext that is unreadable by a human or computer without the proper cipher...
. The operator would next press N, and then X in the same fashion, and so on.
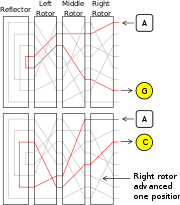
The detailed operation of Enigma is shown in the wiring diagram to the right. To simplify the example, only four components of a complete Enigma machine are shown. In reality, there are 26 lamps and keys, rotor wirings inside the rotors (of which there were either three or four) and between six and ten plug leads.
Kriegsmarine
The Kriegsmarine was the name of the German Navy during the Nazi regime . It superseded the Kaiserliche Marine of World War I and the post-war Reichsmarine. The Kriegsmarine was one of three official branches of the Wehrmacht, the unified armed forces of Nazi Germany.The Kriegsmarine grew rapidly...
M4 and Abwehr variants) installed rotors (5), and entered the reflector (6). The reflector returned the current, via an entirely different path, back through the rotors (5) and entry wheel (4), proceeding through plug 'S' (7) connected with a cable (8) to plug 'D', and another bi-directional switch (9) to light the appropriate lamp.
The repeated changes of electrical path through an Enigma scrambler, implemented a polyalphabetic substitution cipher
Polyalphabetic cipher
A polyalphabetic cipher is any cipher based on substitution, using multiple substitution alphabets. The Vigenère cipher is probably the best-known example of a polyalphabetic cipher, though it is a simplified special case...
which provided Enigma's high security. The diagram on the left shows how the electrical pathway changed with each key depression, which caused rotation of at least the right hand rotor. Current passed into the set of rotors, into and back out of the reflector, and out through the rotors again. The greyed-out lines are some other possible paths within each rotor; these are hard-wired from one side of each rotor to the other. Letter A encrypts differently with consecutive key presses, first to G, and then to C. This is because the right hand rotor has stepped, sending the signal on a completely different route; eventually other rotors will also step with a key press.
Rotors
The rotors (alternatively wheels or drums, Walzen in German) formed the heart of an Enigma machine. Each rotor was a disc approximately 10 cm (3.9 in) in diameter made from hard rubberRubber
Natural rubber, also called India rubber or caoutchouc, is an elastomer that was originally derived from latex, a milky colloid produced by some plants. The plants would be ‘tapped’, that is, an incision made into the bark of the tree and the sticky, milk colored latex sap collected and refined...
or bakelite with brass
Brass
Brass is an alloy of copper and zinc; the proportions of zinc and copper can be varied to create a range of brasses with varying properties.In comparison, bronze is principally an alloy of copper and tin...
spring-loaded pins on one face arranged in a circle; on the other side are a corresponding number of circular electrical contacts. The pins and contacts represent the alphabet
Alphabet
An alphabet is a standard set of letters—basic written symbols or graphemes—each of which represents a phoneme in a spoken language, either as it exists now or as it was in the past. There are other systems, such as logographies, in which each character represents a word, morpheme, or semantic...
— typically the 26 letters A–Z (this will be assumed for the rest of this description). When the rotors were mounted side-by-side on the spindle, the pins of one rotor rest against the contacts of the neighbouring rotor, forming an electrical connection. Inside the body of the rotor, 26 wires connected each pin on one side to a contact on the other in a complex pattern. Most of the rotors were identified by Roman numerals and each issued copy of rotor I was wired identically to all others. The same was true of the special thin beta and gamma rotors used in the M4 naval variant.

Encryption
In cryptography, encryption is the process of transforming information using an algorithm to make it unreadable to anyone except those possessing special knowledge, usually referred to as a key. The result of the process is encrypted information...
— a simple substitution cipher
Substitution cipher
In cryptography, a substitution cipher is a method of encryption by which units of plaintext are replaced with ciphertext according to a regular system; the "units" may be single letters , pairs of letters, triplets of letters, mixtures of the above, and so forth...
. For example, the pin corresponding to the letter E might be wired to the contact for letter T on the opposite face, and so on. The Enigma's complexity, and cryptographic security, came from using several rotors in series (usually three or four) and the regular stepping movement of the rotors, thus implementing a poly-alphabetic substitution cipher.
When placed in an Enigma, each rotor can be set to one of 26 possible positions. When inserted, it can be turned by hand using the grooved finger-wheel which protrudes from the internal Enigma cover when closed. So that the operator can know the rotor's position, each had an alphabet tyre (or letter ring) attached to the outside of the rotor disk, with 26 characters (typically letters); one of these could be seen through the window, thus indicating the rotational position of the rotor. In early Enigma models, the alphabet ring was fixed to the rotor disk. An improvement introduced in later variants was the ability to adjust the alphabet ring relative to the rotor disk. The position of the ring was known as the Ringstellung ("ring setting"), and was a part of the initial setting of an Enigma prior to an operating session. In modern terms it was a part of the initialization vector
Initialization vector
In cryptography, an initialization vector is a fixed-size input to a cryptographic primitive that is typically required to be random or pseudorandom...
.
The rotors each contained a notch (more than one for some rotors) which was used to control rotor stepping. In the military variants, the notches are located on the alphabet ring.
The Army and Air Force Enigmas were used with several rotors; when first issued, there were only three. On 15 December 1938, this changed to five, from which three were chosen for insertion in the machine for a particular operating session. Rotors were marked with Roman numerals
Roman numerals
The numeral system of ancient Rome, or Roman numerals, uses combinations of letters from the Latin alphabet to signify values. The numbers 1 to 10 can be expressed in Roman numerals as:...
to distinguish them: I, II, III, IV and V, all with single notches located at different points on the alphabet ring. This variation was probably intended as a security measure, but ultimately allowed the Polish Clock Method
Clock (cryptography)
In cryptography, the clock was a method devised by Polish mathematician-cryptologist Jerzy Różycki, at the Polish General Staff's Cipher Bureau, to facilitate decrypting German Enigma ciphers.-Method:...
and British Banburismus
Banburismus
Banburismus was a cryptanalytic process developed by Alan Turing at Bletchley Park in England during the Second World War. It was used by Bletchley Park's Hut 8 to help break German Kriegsmarine messages enciphered on Enigma machines. The process used sequential conditional probability to infer...
attacks.
The Naval version of the Wehrmacht
Wehrmacht
The Wehrmacht – from , to defend and , the might/power) were the unified armed forces of Nazi Germany from 1935 to 1945. It consisted of the Heer , the Kriegsmarine and the Luftwaffe .-Origin and use of the term:...
Enigma had always been issued with more rotors than the other services: at first six, then seven, and finally eight. The additional rotors were marked VI, VII and VIII, all with different wiring, and had two notches cut into them resulting in a more frequent turnover. The four-rotor Naval Enigma (M4) machine accommodated an extra rotor in the same space as the three-rotor version. This was accomplished by replacing the original reflector with a thinner one and by adding a special, also thin, fourth rotor. That fourth rotor was one of two types, Beta or Gamma, and never stepped, but it could be manually set to any of its 26 possible positions, one of which made the machine perform identically to the three-rotor machine.
Stepping
To avoid merely implementing a simple (and easily breakable) substitution cipher, every key press caused one or more rotors to step by one twenty-sixth of a full rotation, before the electrical connections were made. This changed the substitution alphabet used for encryption, ensuring that the cryptographic substitution was different at each new rotor position, producing a more formidable polyalphabetic substitution cipherPolyalphabetic cipher
A polyalphabetic cipher is any cipher based on substitution, using multiple substitution alphabets. The Vigenère cipher is probably the best-known example of a polyalphabetic cipher, though it is a simplified special case...
. The stepping mechanism varied slightly from model to model. The right-hand rotor stepped once with each key stroke, and other rotors stepped less frequently.
Turnover

The first five rotors to be introduced (I–V) contained one notch each, while the additional naval rotors VI, VII and VIII each had two notches. The position of the notch on each rotor was determined by the letter ring which could be adjusted in relation to the core containing the interconnections. The points on the rings at which they caused the next wheel to move were as follows.
| Rotor | Turnover position(s) | BP mnemonic |
|---|---|---|
| I | R | Royal |
| II | F | Flags |
| III | W | Wave |
| IV | K | Kings |
| V | A | Above |
| VI, VII and VIII | A and N | | |
The design also included a feature known as double-stepping. This was enabled due to each pawl being aligned with both the ratchet of its rotor and the rotating notched ring of the neighbouring rotor. If a pawl was allowed to engage with a ratchet through alignment with a notch, as it moved forward it would push against both the ratchet and the notch, advancing both rotors at the same time. In a three-rotor machine, the double-stepping would affect rotor two only. This, if in moving forward allowed the ratchet of rotor three to be engaged, would move again on the subsequent keystroke, thus resulting in two consecutive steps. Rotor two also pushes rotor one forward after 26 of its steps, but as rotor one moves forward with every keystroke anyway, there is no double-stepping. This double-stepping caused the rotors to deviate from odometer
Odometer
An odometer or odograph is an instrument that indicates distance traveled by a vehicle, such as a bicycle or automobile. The device may be electronic, mechanical, or a combination of the two. The word derives from the Greek words hodós and métron...
-style regular motion.
With three wheels and only single notches in the first and second wheels, the machine had a period of 26 × 25 × 26 = 16,900 (not 26 × 26 × 26 because of the double-stepping of the second rotor). Historically, messages were limited to a few hundred letters, and so there was no chance of repeating any net combined rotor position during a single message session, and so cryptanalysts were denied a valuable clue to the substitution used.
To make room for the Naval fourth rotors, Beta and Gamma (introduced in 1942), the reflector was changed, by making it much thinner. The special fourth rotors fit into the space made available. No changes were made to the rest of the mechanism, which eased the changeover to the new mode of operation. Since there were only three pawls, the fourth rotor never stepped, but could be manually set into one of its 26 possible positions.
A device that was designed, but not implemented before the war's end, was the Lückenfüllerwalze (gap-fill wheel) which implemented irregular stepping. It allowed field configuration of notches in all 26 positions. If the number of notches was a relative prime
Prime number
A prime number is a natural number greater than 1 that has no positive divisors other than 1 and itself. A natural number greater than 1 that is not a prime number is called a composite number. For example 5 is prime, as only 1 and 5 divide it, whereas 6 is composite, since it has the divisors 2...
of 26 and the number of notches were different for each wheel, the stepping would be more unpredictable. Like the Umkehrwalze-D it also allowed the internal wiring to be reconfigured.
Entry wheel
The current entry wheel (Eintrittswalze in German), or entry statorStator
The stator is the stationary part of a rotor system, found in an electric generator, electric motor and biological rotors.Depending on the configuration of a spinning electromotive device the stator may act as the field magnet, interacting with the armature to create motion, or it may act as the...
, connects the plugboard
Plugboard
A plugboard, or control panel , is an array of jacks, or hubs, into which patch cords can be inserted to complete an electrical circuit. Control panels were used to direct the operation of some unit record equipment...
, if present, or otherwise the keyboard and lampboard, to the rotor assembly. While the exact wiring used is of comparatively little importance to the security, it proved an obstacle in the progress of Polish
Poland
Poland , officially the Republic of Poland , is a country in Central Europe bordered by Germany to the west; the Czech Republic and Slovakia to the south; Ukraine, Belarus and Lithuania to the east; and the Baltic Sea and Kaliningrad Oblast, a Russian exclave, to the north...
cryptanalyst Marian Rejewski
Marian Rejewski
Marian Adam Rejewski was a Polish mathematician and cryptologist who in 1932 solved the plugboard-equipped Enigma machine, the main cipher device used by Germany...
during his deduction of the rotor wirings. The commercial Enigma connects the keys in the order of their sequence on the keyboard: Q
 A, W
A, W B, E
B, E C and so on. However, the military Enigma connects them in straight alphabetical order: A
C and so on. However, the military Enigma connects them in straight alphabetical order: A A, B
A, B B, C
B, C C, and so on. It took an inspired piece of guesswork for Rejewski to realise the modification.
C, and so on. It took an inspired piece of guesswork for Rejewski to realise the modification.Reflector
With the exception of the early Enigma models A and B, the last rotor came before a reflector (German: Umkehrwalze, meaning reversal rotor), a patented feature distinctive of the Enigma family amongst the various rotor machines designed in the period. The reflector connected outputs of the last rotor in pairs, redirecting current back through the rotors by a different route. The reflector ensured that Enigma is self-reciprocal: conveniently, encryption was the same as decryption. However, the reflector also gave Enigma the property that no letter ever encrypted to itself. This was a severe conceptual flaw and a cryptological mistake subsequently exploited by codebreakers.In the commercial Enigma model C, the reflector could be inserted in one of two different positions. In Model D, the reflector could be set in 26 possible positions, although it did not move during encryption. In the Abwehr Enigma, the reflector stepped during encryption in a manner like the other wheels.
In the German Army and Air Force Enigma, the reflector was fixed and did not rotate; there were four versions. The original version was marked A, and was replaced by Umkehrwalze B on 1 November 1937. A third version, Umkehrwalze C was used briefly in 1940, possibly by mistake, and was solved by Hut 6
Hut 6
Hut 6 was a wartime section of Bletchley Park tasked with the solution of German Army and Air Force Enigma machine ciphers. Hut 8, by contrast, attacked Naval Enigma...
. The fourth version, first observed on 2 January 1944, had a rewireable reflector, called Umkehrwalze D, allowing the Enigma operator to alter the connections as part of the key settings.
Plugboard
A cable placed onto the plugboard connected letters up in pairs; for example, E and Q might be a steckered pair. The effect was to swap those letters before and after the main rotor scrambling unit. For example, when an operator presses E, the signal was diverted to Q before entering the rotors. Several such steckered pairs, up to 13, might be used at one time. However, normally only 10 pairs were used at any one time.
Current flowed from the keyboard through the plugboard, and proceeded to the entry-rotor or Eintrittswalze. Each letter on the plugboard had two jacks. Inserting a plug disconnected the upper jack (from the keyboard) and the lower jack (to the entry-rotor) of that letter. The plug at the other end of the crosswired cable was inserted into another letter's jacks, thus switching the connections of the two letters.
Accessories


One feature that was used on some M4 Enigmas was the Schreibmax, a small printer
Computer printer
In computing, a printer is a peripheral which produces a text or graphics of documents stored in electronic form, usually on physical print media such as paper or transparencies. Many printers are primarily used as local peripherals, and are attached by a printer cable or, in most new printers, a...
which could print the 26 letters on a narrow paper ribbon. This did away with the need for a second operator to read the lamps and write the letters down. The Schreibmax was placed on top of the Enigma machine and was connected to the lamp panel. To install the printer, the lamp cover and all light bulbs had to be removed. Besides its convenience, it could improve operational security; the printer could be installed remotely such that the signal officer operating the machine no longer had to see the decrypted plaintext
Plaintext
In cryptography, plaintext is information a sender wishes to transmit to a receiver. Cleartext is often used as a synonym. Before the computer era, plaintext most commonly meant message text in the language of the communicating parties....
information.
Another accessory was the remote lamp panel Fernlesegerät. For machines equipped with the extra panel, the wooden case of the Enigma was wider and could store the extra panel. There was a lamp panel version that could be connected afterwards, but that required, just as with the Schreibmax, that the lamp panel and lightbulbs be removed. The remote panel made it possible for a person to read the decrypted plaintext without the operator seeing it.
In 1944, the Luftwaffe introduced a plugboard switch, called the Uhr (clock). There was a little box, containing a switch with 40 positions. It replaced the standard plugs. After connecting the plugs, as determined in the daily key sheet, the operator turned the switch into one of the 40 positions, each position producing a different combination of plug wiring. Most of these plug connections were, unlike the default plugs, not pair-wise. In one switch position, the Uhr did not swap any letters, but simply emulated the 13 stecker wires with plugs.
Mathematical analysis
The Enigma transformation for each letter can be specified mathematically as a product of permutationPermutation
In mathematics, the notion of permutation is used with several slightly different meanings, all related to the act of permuting objects or values. Informally, a permutation of a set of objects is an arrangement of those objects into a particular order...
s. Assuming a three-rotor German Army/Air Force Enigma, let
 denote the plugboard transformation,
denote the plugboard transformation,  denote that of the reflector, and
denote that of the reflector, and  denote those of the left, middle and right rotors respectively. Then the encryption
denote those of the left, middle and right rotors respectively. Then the encryption  can be expressed as
can be expressed as .
.After each key press, the rotors turn, changing the transformation. For example, if the right hand rotor
 is rotated
is rotated  positions, the transformation becomes
positions, the transformation becomes  , where
, where  is the cyclic permutation
is the cyclic permutationCyclic permutation
A cyclic permutation or circular permutation is a permutation built from one or more sets of elements in cyclic order.The notion "cyclic permutation" is used in different, but related ways:- Definition 1 :right|mapping of permutation...
mapping A to B, B to C, and so forth. Similarly, the middle and left-hand rotors can be represented as
 and
and  rotations of
rotations of  and
and  . The encryption transformation can then be described as
. The encryption transformation can then be described as .
.Operation
 In use, the Enigma required a list of daily key settings as well as a number of auxiliary documents. The procedures for German Naval Enigma were more elaborate and more secure than the procedures used in other services. The Navy codebook
In use, the Enigma required a list of daily key settings as well as a number of auxiliary documents. The procedures for German Naval Enigma were more elaborate and more secure than the procedures used in other services. The Navy codebookCodebook
A codebook is a type of document used for gathering and storing codes. Originally codebooks were often literally books, but today codebook is a byword for the complete record of a series of codes, regardless of physical format.-Cryptography:...
s were also printed in red, water-soluble ink on pink paper so that they could easily be destroyed if they were at risk of being seized by the enemy. The codebook to the right was taken from captured .
In German military usage, communications were divided up into a number of different networks, all using different settings for their Enigma machines. These communication nets were termed keys at Bletchley Park
Bletchley Park
Bletchley Park is an estate located in the town of Bletchley, in Buckinghamshire, England, which currently houses the National Museum of Computing...
, and were assigned code name
Code name
A code name or cryptonym is a word or name used clandestinely to refer to another name or word. Code names are often used for military purposes, or in espionage...
s, such as Red, Chaffinch, and Shark. Each unit operating on a network was assigned a settings list for its Enigma for a period of time. For a message to be correctly encrypted and decrypted, both sender and receiver had to set up their Enigma in the same way; the rotor selection and order, the starting position and the plugboard connections must be identical. All these settings (together the key
Key (cryptography)
In cryptography, a key is a piece of information that determines the functional output of a cryptographic algorithm or cipher. Without a key, the algorithm would produce no useful result. In encryption, a key specifies the particular transformation of plaintext into ciphertext, or vice versa...
in modern terms) must have been established beforehand, and were distributed in codebook
Codebook
A codebook is a type of document used for gathering and storing codes. Originally codebooks were often literally books, but today codebook is a byword for the complete record of a series of codes, regardless of physical format.-Cryptography:...
s.
An Enigma machine's initial state, the cryptographic key
Key (cryptography)
In cryptography, a key is a piece of information that determines the functional output of a cryptographic algorithm or cipher. Without a key, the algorithm would produce no useful result. In encryption, a key specifies the particular transformation of plaintext into ciphertext, or vice versa...
, has several aspects:
- Wheel order (Walzenlage) — the choice of rotors and the order in which they are fitted.
- Initial position of the rotors — chosen by the operator, different for each message.
- Ring settings (Ringstellung) — the position of the alphabet ring relative to the rotor wiring.
- Plug settings (Steckerverbindungen) — the connections of the plugs in the plugboard.
- In very late versions, the wiring of the reconfigurable reflector.
Note that although the ring settings (ringstellung) were a required part of the setup, they did not actually affect the message encryption because the rotors were positioned independently of the rings. The ring settings were only necessary to determine the initial rotor position based on the message setting which was transmitted at the beginning of a message, as described in the "Indicators" section, below. Once the receiver had set his rotors to the indicated positions, the ring settings no longer played any role in the encryption.
In modern cryptographic language, the ring settings did not actually contribute entropy
Information entropy
In information theory, entropy is a measure of the uncertainty associated with a random variable. In this context, the term usually refers to the Shannon entropy, which quantifies the expected value of the information contained in a message, usually in units such as bits...
to the key used for encrypting the message. Rather, the ring settings were part of a separate key (along with the rest of the setup such as wheel order and plug settings) used to encrypt an initialization vector for the message. The session key consisted of the complete setup except for the ring settings, plus the initial rotor positions chosen arbitrarily by the sender (the message setting). The important part of this session key was the rotor positions, not the ring positions. However, by encoding the rotor position into the ring position using the ring settings, additional variability was added to the encryption of the initialization vector.
Enigma was designed to be secure even if the rotor wiring was known to an opponent, although in practice there was considerable effort to keep the wiring secret. If the wiring is secret, the total number of possible configurations has been calculated to be around 10114 (approximately 380 bits); with known wiring and other operational constraints, this is reduced to around 10²³ (76 bits). Users of Enigma were confident of its security because of the large number of possibilities; it was not then feasible for an adversary to even begin to try every possible configuration in a brute force attack
Brute force attack
In cryptography, a brute-force attack, or exhaustive key search, is a strategy that can, in theory, be used against any encrypted data. Such an attack might be utilized when it is not possible to take advantage of other weaknesses in an encryption system that would make the task easier...
.
Indicator
Most of the key was kept constant for a set time period, typically a day. However, a different initial rotor position was used for each message, a concept similar to an initialisation vectorInitialization vector
In cryptography, an initialization vector is a fixed-size input to a cryptographic primitive that is typically required to be random or pseudorandom...
in modern cryptography. The reason for this is that, were a number of messages to be encrypted with identical or near-identical settings (termed in cryptanalysis as being in depth), it would be possible to attack the messages using a statistical procedure such as Friedman's
William F. Friedman
William Frederick Friedman was a US Army cryptographer who ran the research division of the Army's Signals Intelligence Service in the 1930s, and parts of its follow-on services into the 1950s...
Index of coincidence
Index of coincidence
In cryptography, coincidence counting is the technique of putting two texts side-by-side and counting the number of times that identical letters appear in the same position in both texts...
. The starting position for the rotors was transmitted just before the ciphertext, usually after having been enciphered. The exact method used was termed the indicator procedure. It was design weakness and operator sloppiness in these indicator procedures that were two of the main reasons that breaking Enigma messages was possible.

At the receiving end, the operation was reversed. The operator set the machine to the initial settings and typed in the first six letters of the message (XHTLOA). In this example, EINEIN emerged on the lamps. After moving his rotors to EIN, the receiving operator then typed in the rest of the ciphertext, deciphering the message.
The weakness in this indicator scheme came from two factors. First, use of a global ground setting—this was later changed so the operator selected his initial position to encrypt the indicator, and sent the initial position in the clear. The second problem was the repetition of the indicator, which was a serious security flaw. The message setting was encoded twice, resulting in a relation between first and fourth, second and fifth, and third and sixth character. This security problem enabled the Polish Cipher Bureau to break into the pre-war Enigma system as early as 1932. However, from 1940 on, the Germans changed the procedures to increase the security.
During World War II, codebooks were only used each day to set up the rotors, their ring settings and the plugboard. For each message, the operator selected a random start position, let's say WZA, and a random message key, perhaps SXT. He moved the rotors to the WZA start position and encoded the message key SXT. Assume the result was UHL. He then set up the message key, SXT, as the start position and encrypted the message. Next, he transmitted the start position, WZA, the encoded message key, UHL, and then the ciphertext. The receiver set up the start position according to the first trigram, WZA, and decoded the second trigram, UHL, to obtain the SXT message setting. Next, he used this SXT message setting as the start position to decrypt the message. This way, each ground setting was different and the new procedure avoided the security flaw of double encoded message settings.
This procedure was used by Wehrmacht and Luftwaffe only. The Kriegsmarine procedures on sending messages with the Enigma were far more complex and elaborate. Prior to encryption with the Enigma, the message was encoded using the Kurzsignalheft code book. The Kurzsignalheft contained tables to convert sentences into four-letter groups. A great many choices were included, for example, logistic matters such as refueling and rendezvous with supply ships, positions and grid lists, harbor names, countries, weapons, weather conditions, enemy positions and ships, date and time tables. Another codebook contained the Kenngruppen and Spruchschlüssel: the key identification and message key.
Some details
The Army Enigma machine used only the 26 alphabet characters. Signs were replaced with rare character combinations. A space was omitted or replaced with an X. The X was generally used as point or full-stop.Some signs were different in other parts of the armed forces. The Wehrmacht replaced a comma with ZZ and the question sign with FRAGE or FRAQ.
The Kriegsmarine replaced the comma with Y and the question sign with UD. The combination CH, as in "Acht" (eight) or "Richtung" (direction), was replaced with Q (AQT, RIQTUNG). Two, three and four zeros were replaced with CENTA, MILLE and MYRIA.
The Wehrmacht and the Luftwaffe transmitted messages in groups of five characters.
The Kriegsmarine, using the four rotor Enigma, had four-character groups. Frequently-used names or words were to be varied as much as possible. Words like Minensuchboot (minesweeper) could be written as MINENSUCHBOOT, MINBOOT, MMMBOOT or MMM354. To make cryptanalysis harder, it was forbidden to use more than 250 characters in a single message. Longer messages were divided into several parts, each using its own message key.
History of the machine
Far from being a single design, there are numerous models and variants of the Enigma family. The earliest Enigma machines were commercial models dating from the early 1920s. Starting in the mid-1920s, the various branches of the German military began to use Enigma, making a number of changes in order to increase its security. In addition, a number of other nations either adopted or adapted the Enigma design for their own cipher machines. |
Commercial Enigma

Arthur Scherbius
Arthur Scherbius was a German electrical engineer who patented an invention for a mechanical cipher machine, later sold as the Enigma machine.Scherbius was born in Frankfurt am Main and his father was a small businessman...
applied for a patent for a cipher machine using rotors and, with E. Richard Ritter, founded the firm of Scherbius & Ritter. They approached the German Navy and Foreign Office with their design, but neither was interested. They then assigned the patent rights to Gewerkschaft Securitas, who founded the Chiffriermaschinen Aktien-Gesellschaft (Cipher Machines Stock Corporation) on 9 July 1923; Scherbius and Ritter were on the board of directors.
Chiffriermaschinen AG began advertising a rotor machine — Enigma model A — which was exhibited at the Congress of the International Postal Union
Universal Postal Union
The Universal Postal Union is an international organization that coordinates postal policies among member nations, in addition to the worldwide postal system. The UPU contains four bodies consisting of the Congress, the Council of Administration , the Postal Operations Council and the...
in 1923-1924. The machine was heavy and bulky, incorporating a typewriter
Typewriter
A typewriter is a mechanical or electromechanical device with keys that, when pressed, cause characters to be printed on a medium, usually paper. Typically one character is printed per keypress, and the machine prints the characters by making ink impressions of type elements similar to the pieces...
. It measured 65×45×35 cm and weighed about 50 kg (110.2 lb).

The reflector — an idea suggested by Scherbius's colleague Willi Korn — was first introduced in the Enigma C (1926) model. The reflector is a key feature of the Enigma machines.
Model C was smaller and more portable than its predecessors. It lacked a typewriter, relying instead on the operator reading the lamps; hence the alternative name of "glowlamp Enigma" to distinguish from models A and B.
The Enigma C quickly became extinct, giving way to the Enigma D (1927). This version was widely used, with examples going to Sweden
Sweden
Sweden , officially the Kingdom of Sweden , is a Nordic country on the Scandinavian Peninsula in Northern Europe. Sweden borders with Norway and Finland and is connected to Denmark by a bridge-tunnel across the Öresund....
, the Netherlands
Netherlands
The Netherlands is a constituent country of the Kingdom of the Netherlands, located mainly in North-West Europe and with several islands in the Caribbean. Mainland Netherlands borders the North Sea to the north and west, Belgium to the south, and Germany to the east, and shares maritime borders...
, United Kingdom
United Kingdom
The United Kingdom of Great Britain and Northern IrelandIn the United Kingdom and Dependencies, other languages have been officially recognised as legitimate autochthonous languages under the European Charter for Regional or Minority Languages...
, Japan
Japan
Japan is an island nation in East Asia. Located in the Pacific Ocean, it lies to the east of the Sea of Japan, China, North Korea, South Korea and Russia, stretching from the Sea of Okhotsk in the north to the East China Sea and Taiwan in the south...
, Italy
Italy
Italy , officially the Italian Republic languages]] under the European Charter for Regional or Minority Languages. In each of these, Italy's official name is as follows:;;;;;;;;), is a unitary parliamentary republic in South-Central Europe. To the north it borders France, Switzerland, Austria and...
, Spain
Spain
Spain , officially the Kingdom of Spain languages]] under the European Charter for Regional or Minority Languages. In each of these, Spain's official name is as follows:;;;;;;), is a country and member state of the European Union located in southwestern Europe on the Iberian Peninsula...
, United States
United States
The United States of America is a federal constitutional republic comprising fifty states and a federal district...
, and Poland
Poland
Poland , officially the Republic of Poland , is a country in Central Europe bordered by Germany to the west; the Czech Republic and Slovakia to the south; Ukraine, Belarus and Lithuania to the east; and the Baltic Sea and Kaliningrad Oblast, a Russian exclave, to the north...
.
Military Enigma

The keyboard and lampboard contained 29 letters—A-Z, Ä, Ö and Ü—which were arranged alphabetically, as opposed to the QWERTZU ordering. The rotors had 28 contacts, with the letter X wired to bypass the rotors unencrypted.
Three rotors were chosen from a set of five and the reflector could be inserted in one of four different positions, denoted α, β, γ and δ. The machine was revised slightly in July 1933.
By 15 July 1928, the German Army (Reichswehr
Reichswehr
The Reichswehr formed the military organisation of Germany from 1919 until 1935, when it was renamed the Wehrmacht ....
) had introduced their own version of the Enigma—the Enigma G, revised to the Enigma I by June 1930. Enigma I is also known as the Wehrmacht, or "Services" Enigma, and was used extensively by the German military services and other government organisations (such as the railways
Deutsche Reichsbahn-Gesellschaft
The Deutsche Reichsbahn – was the name of the German national railway created from the railways of the individual states of the German Empire following the end of World War I....
), both before and during World War II
World War II
World War II, or the Second World War , was a global conflict lasting from 1939 to 1945, involving most of the world's nations—including all of the great powers—eventually forming two opposing military alliances: the Allies and the Axis...
.
The major difference between Enigma I and commercial Enigma models was the addition of a plugboard to swap pairs of letters, greatly increasing the cryptographic strength of the machine. Other differences included the use of a fixed reflector, and the relocation of the stepping notches from the rotor body to the movable letter rings. The machine measured 28×34×15 cm (11 in×13.5 in×6 in) and weighed around 12 kg (26.5 lb).
By 1930, the Army had suggested that the Navy adopt their machine, citing the benefits of increased security (with the plugboard) and easier interservice communications. The Navy eventually agreed and in 1934 brought into service the Navy version of the Army Enigma, designated Funkschlüssel ' or M3. While the Army used only three rotors at that time, for greater security the Navy specified a choice of three from a possible five.
In December 1938, the Army issued two extra rotors so that the three rotors were chosen from a set of five. In 1938, the Navy added two more rotors, and then another in 1939 to allow a choice of three rotors from a set of eight. In August 1935, the Air Force also introduced the Wehrmacht Enigma for their communications.
A four-rotor Enigma was introduced by the Navy for U-boat traffic on 1 February 1942, called M4 (the network was known as Triton, or Shark to the Allies). The extra rotor was fitted in the same space by splitting the reflector into a combination of a thin reflector and a thin fourth rotor.
There was also a large, eight-rotor printing model, the Enigma II. In 1933 the Polish Cipher Bureau detected that it was in use for high-level military communications, but that it was soon withdrawn from use after it was found to be unreliable and to jam frequently.
The Abwehr
Abwehr
The Abwehr was a German military intelligence organisation from 1921 to 1944. The term Abwehr was used as a concession to Allied demands that Germany's post-World War I intelligence activities be for "defensive" purposes only...
used the Enigma G (the Abwehr Enigma). This Enigma variant was a four-wheel unsteckered machine with multiple notches on the rotors. This model was equipped with a counter which incremented upon each key press, and so is also known as the "counter machine" or the Zählwerk Enigma.
Other countries also used Enigma machines. The Italian Navy adopted the commercial Enigma as "Navy Cipher D"; the Spanish also used commercial Enigma during their Civil War
Spanish Civil War
The Spanish Civil WarAlso known as The Crusade among Nationalists, the Fourth Carlist War among Carlists, and The Rebellion or Uprising among Republicans. was a major conflict fought in Spain from 17 July 1936 to 1 April 1939...
. British codebreakers succeeded in breaking these machines, which lacked a plugboard.
The Swiss used a version of Enigma called model K or Swiss K for military and diplomatic use, which was very similar to the commercial Enigma D. The machine was broken by a number of parties, including Poland, France, Britain and the United States (the latter codenamed it INDIGO). An Enigma T model (codenamed Tirpitz) was manufactured for use by the Japanese.
It has been estimated that 100,000 Enigma machines were constructed. After the end of World War II, the Allies sold captured Enigma machines, still widely considered secure, to a number of developing countries.
Surviving machines

The Deutsches Museum
Deutsches Museum
The Deutsches Museum in Munich, Germany, is the world's largest museum of technology and science, with approximately 1.5 million visitors per year and about 28,000 exhibited objects from 50 fields of science and technology. The museum was founded on June 28, 1903, at a meeting of the Association...
in Munich
Munich
Munich The city's motto is "" . Before 2006, it was "Weltstadt mit Herz" . Its native name, , is derived from the Old High German Munichen, meaning "by the monks' place". The city's name derives from the monks of the Benedictine order who founded the city; hence the monk depicted on the city's coat...
has both the three- and four-rotor German military variants, as well as several older civilian versions. Several Enigma machines are exhibited at National Codes Centre, Bletchley Park
Bletchley Park
Bletchley Park is an estate located in the town of Bletchley, in Buckinghamshire, England, which currently houses the National Museum of Computing...
, England, at the Polish Army Museum
Polish Army Museum
-Newest Exhibition:The Polish Army Museum was not too long ago given the equipment of the lost soldiers from the Presidential Smolensk aircraft crash. The equipment includes the ID Passes, Portable radios, torches, holsters and much more and all in their original state.Museum of the Polish Army is...
in Warsaw, the Armémuseum (Swedish Army Museum) in Stockholm
Stockholm
Stockholm is the capital and the largest city of Sweden and constitutes the most populated urban area in Scandinavia. Stockholm is the most populous city in Sweden, with a population of 851,155 in the municipality , 1.37 million in the urban area , and around 2.1 million in the metropolitan area...
, the National Signals Museum in Finland
Finland
Finland , officially the Republic of Finland, is a Nordic country situated in the Fennoscandian region of Northern Europe. It is bordered by Sweden in the west, Norway in the north and Russia in the east, while Estonia lies to its south across the Gulf of Finland.Around 5.4 million people reside...
, and at the Australian War Memorial
Australian War Memorial
The Australian War Memorial is Australia's national memorial to the members of all its armed forces and supporting organisations who have died or participated in the wars of the Commonwealth of Australia...
and in the foyer of the Defence Signals Directorate
Defence Signals Directorate
Defence Signals Directorate is an Australian government intelligence agency responsible for signals intelligence and information security .-Overview:According to its website, DSD has two principal functions:...
, both in Canberra
Canberra
Canberra is the capital city of Australia. With a population of over 345,000, it is Australia's largest inland city and the eighth-largest city overall. The city is located at the northern end of the Australian Capital Territory , south-west of Sydney, and north-east of Melbourne...
, Australia.
In the United States, Enigma machines can be seen at the Computer History Museum
Computer History Museum
The Computer History Museum is a museum established in 1996 in Mountain View, California, USA. The Museum is dedicated to preserving and presenting the stories and artifacts of the information age, and exploring the computing revolution and its impact on our lives.-History:The museum's origins...
in Mountain View, California
Mountain View, California
-Downtown:Mountain View has a pedestrian-friendly downtown centered on Castro Street. The downtown area consists of the seven blocks of Castro Street from the Downtown Mountain View Station transit center in the north to the intersection with El Camino Real in the south...
, at the National Security Agency's
National Security Agency
The National Security Agency/Central Security Service is a cryptologic intelligence agency of the United States Department of Defense responsible for the collection and analysis of foreign communications and foreign signals intelligence, as well as protecting U.S...
National Cryptologic Museum
National Cryptologic Museum
The National Cryptologic Museum is an American museum of cryptologic history that is affiliated with the National Security Agency . The first public museum in the U.S. Intelligence Community, NCM is located in the former Colony Seven Motel, just two blocks from the NSA headquarters at Fort...
at Fort Meade
Fort George G. Meade
Fort George G. Meade is a United States Army installation that includes the Defense Information School, the United States Army Field Band, and the headquarters of United States Cyber Command, the National Security Agency, and the Defense Courier Service...
, Maryland, where visitors can try their hand at encrypting messages and deciphering code, and two machines that were acquired after the capture of during World War II, are on display at the Museum of Science and Industry
Museum of Science and Industry (Chicago)
The Museum of Science and Industry is located in Chicago, Illinois, USA in Jackson Park, in the Hyde Park neighborhood adjacent to Lake Michigan. It is housed in the former Palace of Fine Arts from the 1893 World's Columbian Exposition...
in Chicago
Chicago
Chicago is the largest city in the US state of Illinois. With nearly 2.7 million residents, it is the most populous city in the Midwestern United States and the third most populous in the US, after New York City and Los Angeles...
, Illinois. The now-defunct San Diego "Computer Museum of America" had an Enigma in its collection, which has since been given to the San Diego State University
San Diego State University
San Diego State University , founded in 1897 as San Diego Normal School, is the largest and oldest higher education facility in the greater San Diego area , and is part of the California State University system...
Library.
A number of machines are also in private hands. Occasionally, Enigma machines are sold at auction; prices of US$40,000 are not unusual. Replicas of the machine are available in various forms, including an exact reconstructed copy of the Naval M4 model, an Enigma implemented in electronics (Enigma-E), various computer software simulators and paper-and-scissors analogues.
A rare Abwehr Enigma machine, designated G312, was stolen from the Bletchley Park museum on 1 April 2000. In September, a man identifying himself as "The Master" sent a note demanding £25,000 and threatened to destroy the machine if the ransom was not paid. In early October 2000, Bletchley Park officials announced that they would pay the ransom but the stated deadline passed with no word from the blackmailer. Shortly afterwards, the machine was sent anonymously to BBC journalist Jeremy Paxman
Jeremy Paxman
Jeremy Dickson Paxman is a British journalist, author and television presenter. He has worked for the BBC since 1977. He is noted for a forthright and abrasive interviewing style, particularly when interrogating politicians...
, but three rotors were missing.
In November 2000, an antiques dealer named Dennis Yates was arrested after telephoning The Sunday Times
The Sunday Times
The Sunday Times is a British Sunday newspaper.The Sunday Times may also refer to:*The Sunday Times *The Sunday Times *The Sunday Times *The Sunday Times...
to arrange the return of the missing parts. The Enigma machine was returned to Bletchley Park after the incident. In October 2001, Yates was sentenced to 10 months in prison after admitting handling the stolen machine and demanding ransom for its return, although he maintained that he was acting as an intermediary for a third party. Yates was released from prison after serving three months.
In October 2008, the Spanish daily newspaper El País reported that 28 Enigma machines had been discovered by chance in an attic of the Army headquarters in Madrid during inventory taking. These 4-rotor commercial machines had helped Franco's Nationalists win the Spanish Civil War
Spanish Civil War
The Spanish Civil WarAlso known as The Crusade among Nationalists, the Fourth Carlist War among Carlists, and The Rebellion or Uprising among Republicans. was a major conflict fought in Spain from 17 July 1936 to 1 April 1939...
because, although the British code breaker Alfred Dilwyn Knox broke the code generated by Franco's Enigma machines in 1937, this was not disclosed to the Republicans and they could not break the code. The Nationalist government continued to use Enigma machines into the 1950s, eventually having a total of 50. Some of the 28 machines are now on display in Spanish military museums.
Derivatives
The Enigma was influential in the field of cipher machine design, and a number of other rotor machines are derived from it. The British TypexTypex
In the history of cryptography, Typex machines were British cipher machines used from 1937. It was an adaptation of the commercial German Enigma with a number of enhancements that greatly increased its security....
was originally derived from the Enigma patents; Typex even includes features from the patent descriptions that were omitted from the actual Enigma machine. Owing to the need for secrecy about its cipher systems, no royalties were paid for the use of the patents by the British government. The Typex implementation of the Enigma transform is not the same as the transform found in almost all of the German or other Axis implementations of the machine.
A Japanese Enigma clone was codenamed GREEN by American cryptographers. Little used, it contained four rotors mounted vertically. In the U.S., cryptologist William Friedman
William F. Friedman
William Frederick Friedman was a US Army cryptographer who ran the research division of the Army's Signals Intelligence Service in the 1930s, and parts of its follow-on services into the 1950s...
designed the M-325
M-325
In the history of cryptography, M-325, also known as SIGFOY, was an American rotor machine designed by William F. Friedman in 1936. Between 1944 and 1946, more than 1,100 machines were deployed within the United States Foreign Service. Its use was discontinued in 1946 because of faults in operation...
, a machine similar to Enigma in logical operation, although not in construction.
A unique rotor machine was constructed in 2002 by Netherlands
Netherlands
The Netherlands is a constituent country of the Kingdom of the Netherlands, located mainly in North-West Europe and with several islands in the Caribbean. Mainland Netherlands borders the North Sea to the north and west, Belgium to the south, and Germany to the east, and shares maritime borders...
-based Tatjana van Vark. This unusual device was inspired by Enigma but makes use of 40-point rotors, allowing letters, numbers and some punctuation to be used; each rotor contains 509 parts.
Machines like the SIGABA
SIGABA
In the history of cryptography, the ECM Mark II was a cipher machine used by the United States for message encryption from World War II until the 1950s...
, NEMA
NEMA (machine)
In the history of cryptography, the NEMA , also designated the T-D , was a 10-wheel rotor machine designed by the Swiss Army during World War II as a replacement for their Enigma machines.-History:The Swiss became aware that their current machine, a commercial Enigma , had been broken by...
, Typex
Typex
In the history of cryptography, Typex machines were British cipher machines used from 1937. It was an adaptation of the commercial German Enigma with a number of enhancements that greatly increased its security....
and so forth, are deliberately not considered to be Enigma derivatives as their internal ciphering functions are not mathematically identical to the Enigma transform.
Several software implementations of Enigma machines do exist, but not all are state machine compliant with the Enigma family. The most commonly used software derivative (that is not compliant with any hardware implementation of the Enigma) is at Enigma.co.de. Many Java applet Enigmas only accept single letter entry, making use difficult even if the applet is Enigma state machine compliant. Technically Enigma@home is the largest scale deployment of a software Enigma, but the decoding software does not implement encipherment making it a derivative (as all original machines could cipher and decipher).
On the other hand, there is a very user-friendly 3-rotor simulator here: http://w1tp.com/enigma/enigma_w.zip where users can select rotors, use the plugboard as well as defining new settings to the rotors and reflectors. The output is in separate windows which can be independently made "invisible" to hide decryption. A 32-bit version of this simulator can be found here : http://membres.lycos.fr/pc1/enigma
A more complex version is here: http://w1tp.com/enigma/EnigmaSim.zip which includes an "autotyping" function which takes plaintext from a clipboard and converts it to cyphertext (or vice-versa) at one of four speeds. The "very fast" option runs through 26 characters in less than one second.
There currently are no known open source projects to implement the Enigma in logic gates using either RTL
Register transfer level
In integrated circuit design, register-transfer level is a level of abstraction used in describing the operation of a synchronous digital circuit...
or VHDL logic gate markup languages.
Fiction
The play Breaking the CodeBreaking the Code
Breaking the Code is a 1986 play by Hugh Whitemore about British mathematician Alan Turing, who was a key player in the breaking of the German Enigma code at Bletchley Park during World War II...
, dramatised by Hugh Whitemore
Hugh Whitemore
Hugh Whitemore is an English playwright and screenwriter.Whitemore studied for the stage at London's Royal Academy of Dramatic Art, where he is now a Member of the Council. He began his writing career in British television with both original teleplays and adaptations of classic works by Charles...
, is about the life and death of Alan Turing
Alan Turing
Alan Mathison Turing, OBE, FRS , was an English mathematician, logician, cryptanalyst, and computer scientist. He was highly influential in the development of computer science, providing a formalisation of the concepts of "algorithm" and "computation" with the Turing machine, which played a...
, who was the central force in continuing to break the Enigma in Britain
United Kingdom
The United Kingdom of Great Britain and Northern IrelandIn the United Kingdom and Dependencies, other languages have been officially recognised as legitimate autochthonous languages under the European Charter for Regional or Minority Languages...
during World War II
World War II
World War II, or the Second World War , was a global conflict lasting from 1939 to 1945, involving most of the world's nations—including all of the great powers—eventually forming two opposing military alliances: the Allies and the Axis...
. Turing was played by Derek Jacobi
Derek Jacobi
Sir Derek George Jacobi, CBE is an English actor and film director.A "forceful, commanding stage presence", Jacobi has enjoyed a highly successful stage career, appearing in such stage productions as Hamlet, Uncle Vanya, and Oedipus the King. He received a Tony Award for his performance in...
, who also played Turing in a 1996 television adaptation of the play. Although it is a drama and thus takes artistic license, it is nonetheless a fundamentally accurate account.
Robert Harris
Robert Harris (novelist)
Robert Dennis Harris is an English novelist. He is a former journalist and BBC television reporter.-Early life:Born in Nottingham, Harris spent his childhood in a small rented house on a Nottingham council estate. His ambition to become a writer arose at an early age, from visits to the local...
's 1995 novel Enigma is set against the backdrop of World War II Bletchley Park
Bletchley Park
Bletchley Park is an estate located in the town of Bletchley, in Buckinghamshire, England, which currently houses the National Museum of Computing...
and cryptologists working to read Naval Enigma in Hut 8
Hut 8
Hut 8 was a section at Bletchley Park tasked with solving German naval Enigma messages. The section was led initially by Alan Turing...
. The book, with substantial changes in plot, was made into the 2001 film Enigma
Enigma (2001 film)
Enigma is a 2001 British film about the Enigma codebreakers of Bletchley Park in World War II. The film, directed by Michael Apted, stars Dougray Scott and Kate Winslet. The film's screenplay was by Tom Stoppard, based on the novel Enigma by Robert Harris...
, directed by Michael Apted
Michael Apted
Michael David Apted, CMG is an English director, producer, writer and actor. He is one of the most prolific British film directors of his generation but is best known for his work on the Up Series of documentaries and the James Bond film The World Is Not Enough.On 29 June 2003 he was elected...
and starring Kate Winslet
Kate Winslet
Kate Elizabeth Winslet is an English actress and occasional singer. She has received multiple awards and nominations. She was the youngest person to accrue six Academy Award nominations, and won the Academy Award for Best Actress for The Reader...
and Dougray Scott
Dougray Scott
-Early life:The son of Elma, a nurse, and Alan Scott, an actor and salesperson, Stephen Dougray Scott was born in Glenrothes, Fife and attended Auchmuty High School...
. The film has been criticized for many historical inaccuracies, including neglect of the role of Poland
Poland
Poland , officially the Republic of Poland , is a country in Central Europe bordered by Germany to the west; the Czech Republic and Slovakia to the south; Ukraine, Belarus and Lithuania to the east; and the Baltic Sea and Kaliningrad Oblast, a Russian exclave, to the north...
's Biuro Szyfrów
Biuro Szyfrów
The Biuro Szyfrów was the interwar Polish General Staff's agency charged with both cryptography and cryptology ....
in breaking the Enigma cipher and showing the British how to do it. The film—like the book—makes a Pole the villain, who seeks to betray the secret of Enigma decryption.
An earlier Polish film dealing with Polish aspects of the subject was the 1979 Sekret Enigmy
Sekret Enigmy
Sekret Enigmy is a Polish historical film. It was released in 1979....
, whose title translates as The Enigma Secret.
Wolfgang Petersen
Wolfgang Petersen
Wolfgang Petersen is a German film director and screenwriter. His films include The NeverEnding Story, Enemy Mine, Outbreak, In the Line of Fire, Air Force One, The Perfect Storm, Troy, and Poseidon...
's 1981 film Das Boot
Das Boot
Das Boot is a 1981 German epic war film written and directed by Wolfgang Petersen, produced by Günter Rohrbach, and starring Jürgen Prochnow, Herbert Grönemeyer, and Klaus Wennemann...
includes an Enigma machine which is evidently a four-rotor Kriegsmarine variant. It appears in many scenes, which probably capture well the flavour of day-to-day Enigma use aboard a World War II
World War II
World War II, or the Second World War , was a global conflict lasting from 1939 to 1945, involving most of the world's nations—including all of the great powers—eventually forming two opposing military alliances: the Allies and the Axis...
U-Boat. The plot of U-571
U-571 (film)
U-571 is a 2000 film directed by Jonathan Mostow, and starring Matthew McConaughey, Bill Paxton, Harvey Keitel, Thomas Kretschmann, Jon Bon Jovi, Jack Noseworthy, Will Estes, and Tom Guiry...
, released in 2000, revolves around an attempt to seize an Enigma machine from a German U-boat.
An Enigma machine makes a very brief appearance in the 1980s TV show Whiz Kids
Whiz Kids (TV series)
Whiz Kids is an American action/adventure television series which aired on CBS for one season during the 1983-1984 television season. The show follows the adventures of a group of four teenagers — Richie, Alice, Hamilton and Jeremy — who are amateur computer experts and detectives...
, episode 12.
Neal Stephenson
Neal Stephenson
Neal Town Stephenson is an American writer known for his works of speculative fiction.Difficult to categorize, his novels have been variously referred to as science fiction, historical fiction, cyberpunk, and postcyberpunk...
's novel Cryptonomicon
Cryptonomicon
Cryptonomicon is a 1999 novel by American author Neal Stephenson. The novel follows the exploits of two groups of people in two different time periods, presented in alternating chapters...
prominently features the Enigma machine and efforts by British and American cryptologists to break variants of it, and portrays the German U-boat
U-boat
U-boat is the anglicized version of the German word U-Boot , itself an abbreviation of Unterseeboot , and refers to military submarines operated by Germany, particularly in World War I and World War II...
command under Karl Dönitz
Karl Dönitz
Karl Dönitz was a German naval commander during World War II. He started his career in the German Navy during World War I. In 1918, while he was in command of , the submarine was sunk by British forces and Dönitz was taken prisoner...
using it in apparently deliberate ignorance of its having been broken.
In the comedy war film All the Queen's Men
All the Queen's Men
All the Queen's Men is a 2001 action comedy war film. It was directed by Stefan Ruzowitzky and stars Matt LeBlanc and Eddie Izzard. The budget was $15,000,000, but the film only earned $22,723 worldwide, yielding an approximate -99.92% return.-Cast:...
, released in 2001 and starring Matt LeBlanc
Matt LeBlanc
Matthew Steven "Matt" LeBlanc is an American actor, best known for his role as Joey Tribbiani on the NBC sitcoms Friends and its spin-off Joey....
alongside Eddie Izzard
Eddie Izzard
Edward John "Eddie" Izzard is a British stand-up comedian and actor. His comedy style takes the form of rambling, whimsical monologue and self-referential pantomime...
, four World War II Allied soldiers are parachuted into Germany, where, dressed as women, they attempt to steal an Enigma machine. They eventually learn that the Allies already had the machine and that the mission was a ruse intended to mislead the Germans into thinking that Enigma was a closed book to the Allies.
EnigmaWarsaw is an outdoor city game in Warsaw
Warsaw
Warsaw is the capital and largest city of Poland. It is located on the Vistula River, roughly from the Baltic Sea and from the Carpathian Mountains. Its population in 2010 was estimated at 1,716,855 residents with a greater metropolitan area of 2,631,902 residents, making Warsaw the 10th most...
organised by StayPoland travel agency. This treasure hunt
Treasure hunt
A treasure hunt is one of many different types of games which can have one or more players who try to find hidden articles, locations or places by using a series of clues. This is a fictional activity; treasure hunting can also be a real life activity. Treasure hunt games may be an indoor or...
game is devised to help the players imagine pre-war Warsaw. EnigmaWarsaw is named to commemorate the pioneering work of Polish cryptographers Marian Rejewski
Marian Rejewski
Marian Adam Rejewski was a Polish mathematician and cryptologist who in 1932 solved the plugboard-equipped Enigma machine, the main cipher device used by Germany...
, Jerzy Różycki
Jerzy Rózycki
Jerzy Witold Różycki was a Polish mathematician and cryptologist who worked at breaking German Enigma-machine ciphers.-Life:Różycki was born in what is now Ukraine, the fourth and youngest child of Zygmunt Różycki, a pharmacist and graduate of Saint Petersburg University, and Wanda, née Benita. ...
, and Henryk Zygalski
Henryk Zygalski
Henryk Zygalski was a Polish mathematician and cryptologist who worked at breaking German Enigma ciphers before and during World War II.-Life:...
at decrypting the Enigma machine cipher.
To Say Nothing of the Dog
To Say Nothing of the Dog
To Say Nothing of the Dog: How We Found the Bishop's Bird Stump at Last is a 1997 comic science fiction novel by Connie Willis. It takes place in the same universe of time-traveling historians she explored in her story Fire Watch and novel Doomsday Book.To Say Nothing of the Dog won both the Hugo...
is a science fiction novel about time traveling historians in which the importance of the Allies obtaining the German Enigma machine is heavily stressed.
In the TV show Sanctuary, the deciphering of the Enigma cipher is credited to Nikola Tesla during the episode "Into the Black", released on June 20, 2011.
Further reading
- Richard J. Aldrich, GCHQ: The Uncensored Story of Britain's Most Secret Intelligence Agency, HarperCollins, July 2010.
- Calvocoressi, PeterPeter CalvocoressiPeter John Ambrose Calvocoressi was a British political author, historian and a former intelligence officer at Bletchley Park during World War II.-Early years:...
. Top Secret Ultra. Baldwin, new edn 2001. 978-0-947712-36-5 - Cave Brown, AnthonyAnthony Cave BrownAnthony Cave Brown was an English-American journalist, espionage non-fiction writer and historian.-Early years:...
. Bodyguard of Lies, 1975. A journalist's sensationalist best-seller that purported to give a history of Enigma decryption and its effect on the outcome of World War II. Worse than worthless on the seminal Polish work that made "UltraUltraUltra was the designation adopted by British military intelligence in June 1941 for wartime signals intelligence obtained by "breaking" high-level encrypted enemy radio and teleprinter communications at the Government Code and Cypher School at Bletchley Park. "Ultra" eventually became the standard...
" possible. See Richard WoytakRichard WoytakRichard Andrew Woytak was an American historian who specialized in European history of the Interbellum and World War II...
, prefatory note (pp. 75–76) to Marian RejewskiMarian RejewskiMarian Adam Rejewski was a Polish mathematician and cryptologist who in 1932 solved the plugboard-equipped Enigma machine, the main cipher device used by Germany...
, "Remarks on Appendix 1 to British Intelligence in the Second World War by F.H. HinsleyHarry HinsleySir Francis Harry Hinsley OBE was an English historian and cryptanalyst. He worked at Bletchley Park during the Second World War and wrote widely on the history of international relations and British Intelligence during the Second World War...
", CryptologiaCryptologiaCryptologia is a journal in cryptography published quarterly since January 1977. Its remit is all aspects of cryptography, but there is a special emphasis on historical aspects of the subject. The founding editors were Brian J. Winkel, David Kahn, Louis Kruh, Cipher A. Deavours and Greg Mellen...
, vol. 6, no. 1 (January 1982), pp. 76–83. - Garliński, JózefJózef GarlinskiJózef Garliński was a Polish historian and prose writer. He wrote many notable books on the history of World War II, some of which were translated into English...
Intercept, Dent, 1979. A superficial, sometimes misleading account of Enigma decryption before and during World War II, of equally slight value as to both the Polish and British phases. See Richard WoytakRichard WoytakRichard Andrew Woytak was an American historian who specialized in European history of the Interbellum and World War II...
and Christopher KasparekChristopher KasparekChristopher Kasparek is a Scottish-born writer of Polish descent who has translated works by Ignacy Krasicki, Bolesław Prus, Florian Znaniecki, Władysław Tatarkiewicz, Marian Rejewski and Władysław Kozaczuk, as well as the Polish-Lithuanian Constitution of May 3, 1791.He has published papers on...
, "The Top Secret of World War II", The Polish ReviewThe Polish ReviewThe Polish Review is an English-language scholarly journal published quarterly in New York City by the Polish Institute of Arts and Sciences of America.The Polish Review has been appearing since 1956.-Editors in Chief:*Stanisław Skrzypek...
, vol. XXVIII, no. 2, 1983, pp. 98–103 (specifically, about Garliński, pp. 101–3). - Herivel, JohnJohn HerivelJohn W. Herivel was a British science historian and former World War II codebreaker at Bletchley Park.As a codebreaker concerned with Cryptanalysis of the Enigma, Herivel is remembered chiefly for the discovery of what was soon dubbed the Herivel tip or Herivelismus...
. Herivelismus and the German military Enigma. Baldwin, 2008. 978-0-947712-46-4 - Keen, John. Harold 'Doc' Keen and the Bletchley Park Bombe. Baldwin, 2003. 978-0-947712-42-6
- Large, Christine. Hijacking Enigma, 2003, ISBN 0-470-86347-1.
- Marks, Philip. "Umkehrwalze D: Enigma's Rewirable Reflector—Part I", Cryptologia 25(2), April 2001, pp. 101–141.
- Marks, Philip. "Umkehrwalze D: Enigma's Rewirable Reflector—Part II", Cryptologia 25(3), July 2001, pp. 177–212.
- Marks, Philip. "Umkehrwalze D: Enigma's Rewirable Reflector—Part III", Cryptologia 25(4), October 2001, pp. 296–310.
- Perera, Tom. The Story of the ENIGMA: History, Technology and Deciphering, 2nd Edition, CD-ROM, 2004, Artifax Books, ISBN 1-890024-06-6 sample pages
- Rejewski, MarianMarian RejewskiMarian Adam Rejewski was a Polish mathematician and cryptologist who in 1932 solved the plugboard-equipped Enigma machine, the main cipher device used by Germany...
. "How Polish Mathematicians Deciphered the Enigma", Annals of the History of Computing 3, 1981. This article is regarded by Andrew Hodges, Alan Turing's biographer, as "the definitive account" (see Hodges' Alan Turing: The Enigma, Walker and Company, 2000 paperback edition, p. 548, footnote 4.5). - Quirantes, Arturo. "Model Z: A Numbers-Only Enigma Version", Cryptologia 28(2), April 2004.
- Sebag-Montefiore, HughHugh Sebag-MontefioreHugh Sebag-Montefiore is a British writer. He trained as a barrister before becoming a journalist and then a non-fiction writer. His second book "Dunkirk: Fight to the Last Man" was published in 2006...
. Enigma: the battle for the code. Cassell Military Paperbacks, London, 2004. 978-1-407-22129-8 - Ulbricht, Heinz. Enigma Uhr, Cryptologia, 23(3), April 1999, pp. 194–205.
- Welchman, GordonGordon WelchmanGordon Welchman was a British-American mathematician, university professor, World War II codebreaker at Bletchley Park, and author.-Education and early career:...
. The Hut Six Story: breaking the Enigma codes. Baldwin, new edition, 1997. 978-0-947712-34-1 - Winterbotham, F.W, The Ultra Secret, Harper and Row, New York, 1974; Spanish edition Ultrasecreto, Ediciones Grijalbo, Madrid, 1975
External links
- Bletchley Park National Code Center Home of the British codebreakers during the Second World War
- Pictures of a four-rotor naval enigma, including Flash (SWF) views of the machine
- Enigma Pictures and Demonstration by NSA Employee at RSA
- An online Enigma Machine simulator
- Online Enigma simulator

