
Protected mode
Encyclopedia
In computing, protected mode, also called protected virtual address mode, is an operational mode of x86-compatible central processing unit
s (CPU). It allows system software
to utilize features such as virtual memory
, paging
, safe multi-tasking
, and other features designed to increase an operating system's control over application software
.
When a processor that supports x86 protected mode is powered on, it begins executing instructions in real mode
, in order to maintain backwards compatibility with earlier x86 processors. Protected mode may only be entered after the system software sets up several descriptor tables and enables the Protection Enable (PE) bit
in the Control Register
0 (CR0).
Protected mode was first added to the x86 architecture
in 1982, with the release of Intel's 80286 (286) processor, and later extended with the release of the 80386 (386) in 1985. Due to the enhancements added by protected mode, it has become widely adopted and has become the foundation for all subsequent enhancements to the x86 architecture.
, the predecessor to the 286, was originally designed with a 20-bit
memory
address bus
. This allowed the processor to access 220 bytes of memory, equivalent to 1 megabyte
. At the time, 1 megabyte was considered a relatively large amount of memory, so the designers of the IBM Personal Computer reserved the first 640 kilobytes for application and the operating system usage and the remaining 384 kilobytes
were reserved for the Basic Input/Output System
(BIOS) and memory for add-on devices
.
As time progressed, the cost of memory continuously decreased and utilization increased. The 1 MB limitation eventually became a significant problem. Intel intended to solve this limitation along with others with the release of the 286.
s, could be accessed at a time.
The 286 maintained backwards compatibility with the previous 8086 by initially entering real mode on power up. Real mode functioned identically to the 8086, allowing older software to run unmodified on the newer 286. To access the extended functionality of the 286, the operating system would set the processor into protected mode. This enabled 24 bit addressing which allowed the processor to access 224 bytes of memory, equivalent to 16 megabyte
s.
.png)
With the release of the 386 in 1985, many of the issues preventing widespread adoption of the previous protected mode were addressed.
The 386 was released with an address bus size of 32 bits, which allows for 232 bytes of memory accessing, equivalent to 4 gigabytes. The segment sizes were also increased to 32 bits, meaning that the full address space of 4 gigabytes could be accessed without the need to switch between multiple segments. In addition to the increased size of the address bus and segment registers, many other new features were added with the intention of increasing operational security and stability.
Protected mode is now used in virtually all modern operating system
s which run on the x86 architecture, such as Microsoft Windows
, Linux
, and many others.
* The 32-bit physical address space is not present on the 80386SX, and other 386 processor variants which use the older 286 bus.
created a workaround which involved resetting the CPU via the keyboard controller and saving the system registers, stack pointer
and often the interrupt mask in the real-time clock chip's RAM. This allowed the BIOS to restore the CPU to a similar state and begin executing code before the reset. Later, a Triple fault
was used to reset the 286 CPU, which was a lot faster and cleaner than the keyboard controller method.
To enter protected mode, the Global Descriptor Table
(GDT) must first be created with a minimum of three entries: a null descriptor, a code segment descriptor and data segment descriptor. The 21st address line
(A20 line) also must be enabled to allow the use of all the address lines so that the CPU can access beyond 1 megabyte of memory (only the first 20 are allowed to be used after power-up to guarantee compatibility with older software). After performing those two steps, the PE bit must be set in the CR0 register and a far jump must be made to clear the prefetch input queue
.
; set PE bit
mov eax, cr0
or eax, 1
mov cr0, eax
; far jump (cs = selector of code segment)
jmp cs:@pm
@pm:
; Now we are in PM.
With the release of the 386, protected mode could be exited by loading the segment registers with real mode values, disabling the A20 line and clearing the PE bit in the CR0 register, without the need to perform the initial setup steps required with the 286.
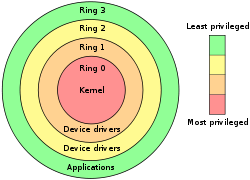 In protected mode, there are four privilege levels or ring
In protected mode, there are four privilege levels or ring
s, numbered from 0 to 3, with ring 0 being the most privileged and 3 being the least. The use of rings allows for system software to restrict tasks from accessing data, call gate
s or executing privileged instructions.
In most environments, the operating system and some device driver
s run in ring 0 and applications run in ring 3.
For the most part, the binary compatibility with real-mode code, the ability to access up to 16 MB of physical memory, and 1 GB of virtual memory
, were the most apparent changes to application programmers. This was not without its limitations, if an application utilized or relied on any of the techniques below it wouldn't run:
In reality, almost all DOS
application programs violated these rules. Due to these limitations, virtual 8086 mode
was created and released with the 386. Despite such potential setbacks, Windows 3.0
and its successors can take advantage of the binary compatibility with real mode to run many Windows 2.x (Windows 2.0
and Windows 2.1x
) applications, which run in real mode in Windows 2.x, in protected mode.
will generate an exception
that must be served by the operating system. In addition, applications running in virtual 8086 mode generate a trap
with the use of instructions that involve input/output
(I/O), which can negatively impact performance.
Due to these limitations, some programs originally designed to run on the 8086 cannot be run in virtual 8086 mode. As a result, system software is forced to either compromise system security or backwards compatibility when dealing with legacy software
. An example of such a compromise can be seen with the release of Windows NT
, which dropped backwards compatibility for "ill-behaved" DOS applications.
In real mode each logical address points directly into physical memory location,
every logical address consists of two 16 bit parts:
The segment part of the logical address contains the base address of a segment with a granularity of 16 bytes,
i.e. a segments may start at physical address 0, 16, 32, ..., 220-16.
The offset part of the logical address contains an offset inside the segment,
i.e. the physical address can be calculated as
physical_address := segment_part × 16 + offset (if the address line A20
is enabled),
respectively (segment_part × 16 + offset) mod 220 (if A20 is off)
Every segment has a size of 216 bytes.
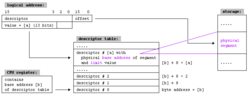
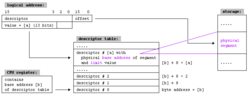
the 13 upper bits (bit 3 to bit 15) of the selector contains the index of an entry inside a descriptor table. The lowest two bits define the privilege of the request, from 0 to 3 where 0 has the highest priority and 3 the lowest. The remainder bit specifies if the operation is against the GDT or a LDT.
The descriptor table entry contains
so every byte of the physical memory can be defined as bound of the segment.
The limit value inside the descriptor table entry has a length of 16 bits
so segment length can be between 1 byte and 216 byte.
The calculated linear address equals the physical memory address.
so every byte of the physical memory can be defined as bound of the segment.
The limit value inside the descriptor table entry is expanded to 20 bits
and completed with a granularity flag (shortly: G-bit):
If paging is off (see below), the calculated linear address equals the physical memory address.
If paging is on, the calculated linear address is used as input of paging.
The 386 processor also uses 32 bit values for the address offset.
For maintaining compatibility with 286 protected mode a new default flag (shortly D-bit) was added.
If D-bit of a code segment is off all commands inside this segment will be interpreted as 16 bit commands.
Columns B: Byte offset inside entry
Column bits, first range: Bit offset inside entry
Column bits, second range: Bit offset inside byte
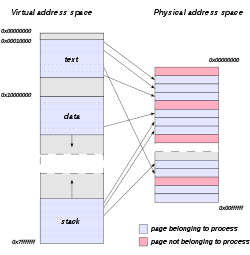

In addition to adding virtual 8086 mode, the 386 also added paging to protected mode. Through paging, system software can restrict and control a task's access to pages, which are sections of memory. In many operating systems, paging is used to create an independent virtual address space for each task. This prevents one task from manipulating the memory of another. Paging also allows for pages to be moved out of primary storage and onto a slower and larger secondary storage, such as a hard disk
. This allows for more memory to be used than physically available in primary storage. The x86 architecture allows control of pages through two arrays: page directories and page table
s.
Originally, a page directory was the size of one page, 4 kilobytes, and contained 1,024 page directory entries (PDE), although subsequent enhancements to the x86 architecture have added the ability to use larger page sizes. Each PDE contained a pointer to a page table. A page table was also originally 4 kilobytes in size and contained 1,024 page table entries (PTE). Each PTE contained a pointer to the actual page's physical address and are only used when 4 kilobyte pages are used. At any given time, only one page directory may be in active use.
, and the Task State Segment
(TSS), introduced with the 286, preemptive
multitasking
was made possible on the x86 architecture. The TSS allows general-purpose registers, segment selector fields, and stacks to all be modified without affecting those of another task. The TSS also allows a task's privilege level, and I/O port permissions to be independent of another task's.
In many operating systems, the full features of the TSS are not used. This is commonly due to portability concerns or due to the performance issues created with hardware task switches. As a result many operating systems use both hardware and software to create a multitasking system.
1.x try to switch the processor between protected and real modes. This is both slow and unsafe, because a real mode program can easily crash
a computer. OS/2 1.x defines restrictive programming rules allowing a Family API or bound program to run in either real or protected mode.
Some early Unix
operating systems, OS/2
1.x, and Windows used this mode. Windows 3.0
was able to run real mode programs in 16-bit protected mode. Windows 3.0
, when switching to protected mode, decided to preserve the single privilege level model that was used in real mode, which is why Windows applications and DLLs can hook interrupts and do direct hardware access. That lasted through the Windows 9x
series. If a Windows 1.x or 2.x program is written properly and avoids segment arithmetic, it will run the same way in both real and protected modes. Windows programs generally avoid segment arithmetic because Windows implements a software virtual memory scheme, moving program code and data in memory when programs are not running, so manipulating absolute addresses is dangerous; programs should only keep handle
s to memory blocks when not running. Starting an old program while Windows 3.0 is running in protected mode triggers a warning dialog, suggesting to either run Windows in real mode or to obtain an updated version of the application. Updating well-behaved programs using the MARK utility with the MEMORY parameter avoids this dialog. It is not possible to have some GUI programs running in 16-bit protected mode and other GUI programs running in real mode. In Windows 3.1 real mode disappeared.
Today, 16-bit protected mode is still used for running applications, e.g. DPMI compatible DOS extender
programs (through virtual DOS machine
s) or Windows 3.x applications (through the Windows on Windows
subsystem) and certain classes of device driver
s (e.g. for changing the screen-resolution using BIOS functionality) in OS/2 2.0 and later, all under control of a 32-bit kernel.
Central processing unit
The central processing unit is the portion of a computer system that carries out the instructions of a computer program, to perform the basic arithmetical, logical, and input/output operations of the system. The CPU plays a role somewhat analogous to the brain in the computer. The term has been in...
s (CPU). It allows system software
System software
System software is computer software designed to operate the computer hardware and to provide a platform for running application software.The most basic types of system software are:...
to utilize features such as virtual memory
Virtual memory
In computing, virtual memory is a memory management technique developed for multitasking kernels. This technique virtualizes a computer architecture's various forms of computer data storage , allowing a program to be designed as though there is only one kind of memory, "virtual" memory, which...
, paging
Paging
In computer operating systems, paging is one of the memory-management schemes by which a computer can store and retrieve data from secondary storage for use in main memory. In the paging memory-management scheme, the operating system retrieves data from secondary storage in same-size blocks called...
, safe multi-tasking
Computer multitasking
In computing, multitasking is a method where multiple tasks, also known as processes, share common processing resources such as a CPU. In the case of a computer with a single CPU, only one task is said to be running at any point in time, meaning that the CPU is actively executing instructions for...
, and other features designed to increase an operating system's control over application software
Application software
Application software, also known as an application or an "app", is computer software designed to help the user to perform specific tasks. Examples include enterprise software, accounting software, office suites, graphics software and media players. Many application programs deal principally with...
.
When a processor that supports x86 protected mode is powered on, it begins executing instructions in real mode
Real mode
Real mode, also called real address mode, is an operating mode of 80286 and later x86-compatible CPUs. Real mode is characterized by a 20 bit segmented memory address space and unlimited direct software access to all memory, I/O addresses and peripheral hardware...
, in order to maintain backwards compatibility with earlier x86 processors. Protected mode may only be entered after the system software sets up several descriptor tables and enables the Protection Enable (PE) bit
Bit
A bit is the basic unit of information in computing and telecommunications; it is the amount of information stored by a digital device or other physical system that exists in one of two possible distinct states...
in the Control Register
Control register
A control register is a processor register which changes or controls the general behavior of a CPU or other digital device. Common tasks performed by control registers include interrupt control, switching the addressing mode, paging control, and coprocessor control.-CR0:The CR0 register is 32 bits...
0 (CR0).
Protected mode was first added to the x86 architecture
X86 architecture
The term x86 refers to a family of instruction set architectures based on the Intel 8086 CPU. The 8086 was launched in 1978 as a fully 16-bit extension of Intel's 8-bit based 8080 microprocessor and also introduced segmentation to overcome the 16-bit addressing barrier of such designs...
in 1982, with the release of Intel's 80286 (286) processor, and later extended with the release of the 80386 (386) in 1985. Due to the enhancements added by protected mode, it has become widely adopted and has become the foundation for all subsequent enhancements to the x86 architecture.
History
The 8086Intel 8086
The 8086 is a 16-bit microprocessor chip designed by Intel between early 1976 and mid-1978, when it was released. The 8086 gave rise to the x86 architecture of Intel's future processors...
, the predecessor to the 286, was originally designed with a 20-bit
Bit
A bit is the basic unit of information in computing and telecommunications; it is the amount of information stored by a digital device or other physical system that exists in one of two possible distinct states...
memory
Computer storage
Computer data storage, often called storage or memory, refers to computer components and recording media that retain digital data. Data storage is one of the core functions and fundamental components of computers....
address bus
Address bus
An address bus is a computer bus that is used to specify a physical address. When a processor or DMA-enabled device needs to read or write to a memory location, it specifies that memory location on the address bus...
. This allowed the processor to access 220 bytes of memory, equivalent to 1 megabyte
Megabyte
The megabyte is a multiple of the unit byte for digital information storage or transmission with two different values depending on context: bytes generally for computer memory; and one million bytes generally for computer storage. The IEEE Standards Board has decided that "Mega will mean 1 000...
. At the time, 1 megabyte was considered a relatively large amount of memory, so the designers of the IBM Personal Computer reserved the first 640 kilobytes for application and the operating system usage and the remaining 384 kilobytes
Upper Memory Area
In DOS memory management, the upper memory area refers to memory between the addresses of 640 KB and 1024 KB in an IBM PC or compatible. IBM reserved the uppermost 384 KB of the 8088 CPU's 1024 KB address space for ROM, RAM on peripherals, and memory-mapped input/output...
were reserved for the Basic Input/Output System
BIOS
In IBM PC compatible computers, the basic input/output system , also known as the System BIOS or ROM BIOS , is a de facto standard defining a firmware interface....
(BIOS) and memory for add-on devices
Peripheral
A peripheral is a device attached to a host computer, but not part of it, and is more or less dependent on the host. It expands the host's capabilities, but does not form part of the core computer architecture....
.
As time progressed, the cost of memory continuously decreased and utilization increased. The 1 MB limitation eventually became a significant problem. Intel intended to solve this limitation along with others with the release of the 286.
The 286
The initial protected mode, released with the 286, was not widely used. Several shortcomings such as the inability to access the BIOS and the inability to switch back to real mode without resetting the processor prevented widespread usage. Widespread acceptance was additionally hampered by the fact that the 286 only allowed memory access in 16 bit segments, meaning only 216 bytes, equivalent to 64 kilobyteKilobyte
The kilobyte is a multiple of the unit byte for digital information. Although the prefix kilo- means 1000, the term kilobyte and symbol KB have historically been used to refer to either 1024 bytes or 1000 bytes, dependent upon context, in the fields of computer science and information...
s, could be accessed at a time.
The 286 maintained backwards compatibility with the previous 8086 by initially entering real mode on power up. Real mode functioned identically to the 8086, allowing older software to run unmodified on the newer 286. To access the extended functionality of the 286, the operating system would set the processor into protected mode. This enabled 24 bit addressing which allowed the processor to access 224 bytes of memory, equivalent to 16 megabyte
Megabyte
The megabyte is a multiple of the unit byte for digital information storage or transmission with two different values depending on context: bytes generally for computer memory; and one million bytes generally for computer storage. The IEEE Standards Board has decided that "Mega will mean 1 000...
s.
The 386
.png)
With the release of the 386 in 1985, many of the issues preventing widespread adoption of the previous protected mode were addressed.
The 386 was released with an address bus size of 32 bits, which allows for 232 bytes of memory accessing, equivalent to 4 gigabytes. The segment sizes were also increased to 32 bits, meaning that the full address space of 4 gigabytes could be accessed without the need to switch between multiple segments. In addition to the increased size of the address bus and segment registers, many other new features were added with the intention of increasing operational security and stability.
Protected mode is now used in virtually all modern operating system
Operating system
An operating system is a set of programs that manage computer hardware resources and provide common services for application software. The operating system is the most important type of system software in a computer system...
s which run on the x86 architecture, such as Microsoft Windows
Microsoft Windows
Microsoft Windows is a series of operating systems produced by Microsoft.Microsoft introduced an operating environment named Windows on November 20, 1985 as an add-on to MS-DOS in response to the growing interest in graphical user interfaces . Microsoft Windows came to dominate the world's personal...
, Linux
Linux
Linux is a Unix-like computer operating system assembled under the model of free and open source software development and distribution. The defining component of any Linux system is the Linux kernel, an operating system kernel first released October 5, 1991 by Linus Torvalds...
, and many others.
386 additions to protected mode
With the release of the 386, the following additional features were added to protected mode:- PagingPagingIn computer operating systems, paging is one of the memory-management schemes by which a computer can store and retrieve data from secondary storage for use in main memory. In the paging memory-management scheme, the operating system retrieves data from secondary storage in same-size blocks called...
- 32-bit32-bitThe range of integer values that can be stored in 32 bits is 0 through 4,294,967,295. Hence, a processor with 32-bit memory addresses can directly access 4 GB of byte-addressable memory....
physical and virtual address spaceAddress spaceIn computing, an address space defines a range of discrete addresses, each of which may correspond to a network host, peripheral device, disk sector, a memory cell or other logical or physical entity.- Overview :...
* - 32-bit segmentMemory segmentx86 memory segmentation refers to the implementation of memory segmentation on the x86 architecture. Memory is divided into portions that may be addressed by a single index register without changing a 16-bit segment selector. In real mode or V86 mode, a segment is always 64 kilobytes in size . In...
offsets - Ability to switch back to real mode
- Virtual 8086 modeVirtual 8086 modeIn the 80386 microprocessor and later, virtual 8086 mode allows the execution of real mode applications that are incapable of running directly in protected mode while the processor is running a protected mode operating system.VM86 mode uses a segmentation scheme identical to that of real mode In...
Entering and exiting protected mode
Until the release of the 386, protected mode did not offer a direct method to switch back into real mode once protected mode was entered. IBMIBM
International Business Machines Corporation or IBM is an American multinational technology and consulting corporation headquartered in Armonk, New York, United States. IBM manufactures and sells computer hardware and software, and it offers infrastructure, hosting and consulting services in areas...
created a workaround which involved resetting the CPU via the keyboard controller and saving the system registers, stack pointer
Call stack
In computer science, a call stack is a stack data structure that stores information about the active subroutines of a computer program. This kind of stack is also known as an execution stack, control stack, run-time stack, or machine stack, and is often shortened to just "the stack"...
and often the interrupt mask in the real-time clock chip's RAM. This allowed the BIOS to restore the CPU to a similar state and begin executing code before the reset. Later, a Triple fault
Triple fault
A triple fault is a special kind of exception generated by the CPU when an exception occurs while the CPU is trying to invoke the double fault exception handler, which itself handles exceptions occurring while trying to invoke a regular exception handler....
was used to reset the 286 CPU, which was a lot faster and cleaner than the keyboard controller method.
To enter protected mode, the Global Descriptor Table
Global Descriptor Table
The Global Descriptor Table or GDT is a data structure used by Intel x86-family processors starting with the 80286 in order to define the characteristics of the various memory areas used during program execution, including the base address, the size and access privileges like executability and...
(GDT) must first be created with a minimum of three entries: a null descriptor, a code segment descriptor and data segment descriptor. The 21st address line
A20 line
The A20 or addressing line 20 is one of the plethora of electrical lines that make up the system bus of an x86-based computer system. The A20 line in particular is used to transmit the 21st bit on the address bus....
(A20 line) also must be enabled to allow the use of all the address lines so that the CPU can access beyond 1 megabyte of memory (only the first 20 are allowed to be used after power-up to guarantee compatibility with older software). After performing those two steps, the PE bit must be set in the CR0 register and a far jump must be made to clear the prefetch input queue
Prefetch input queue
Fetching the instruction opcodes from program memory well in advance is known as prefetching and it is served by using prefetch input queue .The pre-fetched instructions are stored in data structure Queue. The fetching of opcodes well in advance, prior to their need for execution increases the...
.
; set PE bit
mov eax, cr0
or eax, 1
mov cr0, eax
; far jump (cs = selector of code segment)
jmp cs:@pm
@pm:
; Now we are in PM.
With the release of the 386, protected mode could be exited by loading the segment registers with real mode values, disabling the A20 line and clearing the PE bit in the CR0 register, without the need to perform the initial setup steps required with the 286.
Features
Protected mode has a number of features designed to enhance an operating system's control over application software, in order to increase security and system stability. These additions allow the operating system to function in a way that would be significantly more difficult or even impossible without proper hardware support.Privilege levels
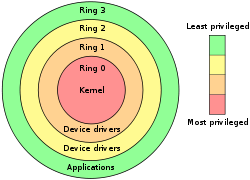
Ring (computer security)
In computer science, hierarchical protection domains, often called protection rings, are a mechanism to protect data and functionality from faults and malicious behaviour . This approach is diametrically opposite to that of capability-based security.Computer operating systems provide different...
s, numbered from 0 to 3, with ring 0 being the most privileged and 3 being the least. The use of rings allows for system software to restrict tasks from accessing data, call gate
Call gate
A call gate is a mechanism in Intel's x86 architecture for changing the privilege level of the CPU when it executes a predefined function call using a CALL FAR instruction.- Overview :...
s or executing privileged instructions.
In most environments, the operating system and some device driver
Device driver
In computing, a device driver or software driver is a computer program allowing higher-level computer programs to interact with a hardware device....
s run in ring 0 and applications run in ring 3.
Real mode application compatibility
According to the Intel 80286 Programmer's Reference Manual,For the most part, the binary compatibility with real-mode code, the ability to access up to 16 MB of physical memory, and 1 GB of virtual memory
Virtual memory
In computing, virtual memory is a memory management technique developed for multitasking kernels. This technique virtualizes a computer architecture's various forms of computer data storage , allowing a program to be designed as though there is only one kind of memory, "virtual" memory, which...
, were the most apparent changes to application programmers. This was not without its limitations, if an application utilized or relied on any of the techniques below it wouldn't run:
- Segment arithmetic
- Privileged instructions
- Direct hardware access
- Writing to a code segmentSelf-modifying codeIn computer science, self-modifying code is code that alters its own instructions while it is executing - usually to reduce the instruction path length and improve performance or simply to reduce otherwise repetitively similar code, thus simplifying maintenance...
- Executing data
- Overlapping segments
- Use of BIOS functions, due to the BIOS interrupts being reserved by Intel
In reality, almost all DOS
DOS
DOS, short for "Disk Operating System", is an acronym for several closely related operating systems that dominated the IBM PC compatible market between 1981 and 1995, or until about 2000 if one includes the partially DOS-based Microsoft Windows versions 95, 98, and Millennium Edition.Related...
application programs violated these rules. Due to these limitations, virtual 8086 mode
Virtual 8086 mode
In the 80386 microprocessor and later, virtual 8086 mode allows the execution of real mode applications that are incapable of running directly in protected mode while the processor is running a protected mode operating system.VM86 mode uses a segmentation scheme identical to that of real mode In...
was created and released with the 386. Despite such potential setbacks, Windows 3.0
Windows 3.0
Windows 3.0, a graphical environment, is the third major release of Microsoft Windows, and was released on 22 May 1990. It became the first widely successful version of Windows and a rival to Apple Macintosh and the Commodore Amiga on the GUI front...
and its successors can take advantage of the binary compatibility with real mode to run many Windows 2.x (Windows 2.0
Windows 2.0
Windows 2.0 is a 16-bit Microsoft Windows GUI-based operating environment that was released on December 9, 1987 and is the successor to Windows 1.0. With Windows 2.1x in 1988, Windows 2.0 was supplemented by Windows/286 and Windows/386...
and Windows 2.1x
Windows 2.1x
Windows 2.1x is a family of Microsoft Windows graphical user interface-based operating environments.Windows/286 2.10 and Windows/386 2.10 were released on May 27, 1988, less than a year after the release of Windows 2.0...
) applications, which run in real mode in Windows 2.x, in protected mode.
Virtual 8086 mode
With the release of the 386, protected mode offers what the Intel manuals call virtual 8086 mode. Virtual 8086 mode is designed to allow code previously written for the 8086 to run unmodified and concurrently with other tasks, without compromising security or system stability. Virtual 8086 mode, however, is not completely backwards compatible with all programs. Programs that require segment manipulation, privileged instructions, direct hardware access, or use self-modifying codeSelf-modifying code
In computer science, self-modifying code is code that alters its own instructions while it is executing - usually to reduce the instruction path length and improve performance or simply to reduce otherwise repetitively similar code, thus simplifying maintenance...
will generate an exception
Exception handling
Exception handling is a programming language construct or computer hardware mechanism designed to handle the occurrence of exceptions, special conditions that change the normal flow of program execution....
that must be served by the operating system. In addition, applications running in virtual 8086 mode generate a trap
Trap (computing)
In computing and operating systems, a trap, also known as an exception or a fault, is typicallyThere is a wide variation in the nomenclature...
with the use of instructions that involve input/output
Input/output
In computing, input/output, or I/O, refers to the communication between an information processing system , and the outside world, possibly a human, or another information processing system. Inputs are the signals or data received by the system, and outputs are the signals or data sent from it...
(I/O), which can negatively impact performance.
Due to these limitations, some programs originally designed to run on the 8086 cannot be run in virtual 8086 mode. As a result, system software is forced to either compromise system security or backwards compatibility when dealing with legacy software
Legacy system
A legacy system is an old method, technology, computer system, or application program that continues to be used, typically because it still functions for the users' needs, even though newer technology or more efficient methods of performing a task are now available...
. An example of such a compromise can be seen with the release of Windows NT
Windows NT
Windows NT is a family of operating systems produced by Microsoft, the first version of which was released in July 1993. It was a powerful high-level-language-based, processor-independent, multiprocessing, multiuser operating system with features comparable to Unix. It was intended to complement...
, which dropped backwards compatibility for "ill-behaved" DOS applications.
Segment addressing
In real mode each logical address points directly into physical memory location,
every logical address consists of two 16 bit parts:
The segment part of the logical address contains the base address of a segment with a granularity of 16 bytes,
i.e. a segments may start at physical address 0, 16, 32, ..., 220-16.
The offset part of the logical address contains an offset inside the segment,
i.e. the physical address can be calculated as
physical_address := segment_part × 16 + offset (if the address line A20
A20 line
The A20 or addressing line 20 is one of the plethora of electrical lines that make up the system bus of an x86-based computer system. The A20 line in particular is used to transmit the 21st bit on the address bus....
is enabled),
respectively (segment_part × 16 + offset) mod 220 (if A20 is off)
Every segment has a size of 216 bytes.
Protected mode
In protected mode the segment_part is replaced by a 16 bit selector,the 13 upper bits (bit 3 to bit 15) of the selector contains the index of an entry inside a descriptor table. The lowest two bits define the privilege of the request, from 0 to 3 where 0 has the highest priority and 3 the lowest. The remainder bit specifies if the operation is against the GDT or a LDT.
The descriptor table entry contains
- the real linear address of the segment
- a limit value for the segment size
- some attribute bits (flags)
286
The segment address inside the descriptor table entry has a length of 24 bitsso every byte of the physical memory can be defined as bound of the segment.
The limit value inside the descriptor table entry has a length of 16 bits
so segment length can be between 1 byte and 216 byte.
The calculated linear address equals the physical memory address.
386
The segment address inside the descriptor table entry is expanded to 32 bitsso every byte of the physical memory can be defined as bound of the segment.
The limit value inside the descriptor table entry is expanded to 20 bits
and completed with a granularity flag (shortly: G-bit):
- if G-bit is zero limit has a granularity of 1 byte, i.e. segment size may be 1, 2, ..., 220 bytes.
- if G-bit is one limit has a granularity of 212 bytes, i.e. segment size may be 1 × 212, 2 × 212, ..., 220 × 212 bytes.
If paging is off (see below), the calculated linear address equals the physical memory address.
If paging is on, the calculated linear address is used as input of paging.
The 386 processor also uses 32 bit values for the address offset.
For maintaining compatibility with 286 protected mode a new default flag (shortly D-bit) was added.
If D-bit of a code segment is off all commands inside this segment will be interpreted as 16 bit commands.
Structure of segment descriptor entry
| B | bits | 80286 | 80386 | B |
|---|---|---|---|---|
| 0 | 00..07,0..7 | limit | bits 0..15 of limit | 0 |
| 1 | 08..15,0..7 | 1 | ||
| 2 | 16..23,0..7 | base address | bits 0..23 of base address | 2 |
| 3 | 24..31,0..7 | 3 | ||
| 4 | 32..39,0..7 | 4 | ||
| 5 | 40..47,0..7 | attribute flags #1 | 5 | |
| 6 | 48..51,0..3 | unused | bits 16..19 of limit | 6 |
| 52..55,4..7 | attribute flags #2 | |||
| 7 | 56..63,0..7 | bits 24..31 of base address | 7 | |
Columns B: Byte offset inside entry
Column bits, first range: Bit offset inside entry
Column bits, second range: Bit offset inside byte
| attribute flags #2 | ||
|---|---|---|
| 52 | 4 | unused, available for operating system |
| 53 | 5 | reserved, should be zero |
| 54 | 6 | default flag / D-bit |
| 55 | 7 | granularity flag / G-bit |
Paging
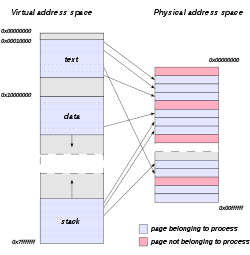

In addition to adding virtual 8086 mode, the 386 also added paging to protected mode. Through paging, system software can restrict and control a task's access to pages, which are sections of memory. In many operating systems, paging is used to create an independent virtual address space for each task. This prevents one task from manipulating the memory of another. Paging also allows for pages to be moved out of primary storage and onto a slower and larger secondary storage, such as a hard disk
Hard disk
A hard disk drive is a non-volatile, random access digital magnetic data storage device. It features rotating rigid platters on a motor-driven spindle within a protective enclosure. Data is magnetically read from and written to the platter by read/write heads that float on a film of air above the...
. This allows for more memory to be used than physically available in primary storage. The x86 architecture allows control of pages through two arrays: page directories and page table
Page table
A page table is the data structure used by a virtual memory system in a computer operating system to store the mapping between virtual addresses and physical addresses. Virtual addresses are those unique to the accessing process...
s.
Originally, a page directory was the size of one page, 4 kilobytes, and contained 1,024 page directory entries (PDE), although subsequent enhancements to the x86 architecture have added the ability to use larger page sizes. Each PDE contained a pointer to a page table. A page table was also originally 4 kilobytes in size and contained 1,024 page table entries (PTE). Each PTE contained a pointer to the actual page's physical address and are only used when 4 kilobyte pages are used. At any given time, only one page directory may be in active use.
Multitasking
Through the use of the rings, privileged call gatesCall gate
A call gate is a mechanism in Intel's x86 architecture for changing the privilege level of the CPU when it executes a predefined function call using a CALL FAR instruction.- Overview :...
, and the Task State Segment
Task State Segment
The task state segment is a special structure on x86-based computers which holds information about a task. It is used by the operating system kernel for task management...
(TSS), introduced with the 286, preemptive
Preemption (computing)
In computing, preemption is the act of temporarily interrupting a task being carried out by a computer system, without requiring its cooperation, and with the intention of resuming the task at a later time. Such a change is known as a context switch...
multitasking
Computer multitasking
In computing, multitasking is a method where multiple tasks, also known as processes, share common processing resources such as a CPU. In the case of a computer with a single CPU, only one task is said to be running at any point in time, meaning that the CPU is actively executing instructions for...
was made possible on the x86 architecture. The TSS allows general-purpose registers, segment selector fields, and stacks to all be modified without affecting those of another task. The TSS also allows a task's privilege level, and I/O port permissions to be independent of another task's.
In many operating systems, the full features of the TSS are not used. This is commonly due to portability concerns or due to the performance issues created with hardware task switches. As a result many operating systems use both hardware and software to create a multitasking system.
Operating systems
Operating systems like OS/2OS/2
OS/2 is a computer operating system, initially created by Microsoft and IBM, then later developed by IBM exclusively. The name stands for "Operating System/2," because it was introduced as part of the same generation change release as IBM's "Personal System/2 " line of second-generation personal...
1.x try to switch the processor between protected and real modes. This is both slow and unsafe, because a real mode program can easily crash
Crash (computing)
A crash in computing is a condition where a computer or a program, either an application or part of the operating system, ceases to function properly, often exiting after encountering errors. Often the offending program may appear to freeze or hang until a crash reporting service documents...
a computer. OS/2 1.x defines restrictive programming rules allowing a Family API or bound program to run in either real or protected mode.
Some early Unix
Unix
Unix is a multitasking, multi-user computer operating system originally developed in 1969 by a group of AT&T employees at Bell Labs, including Ken Thompson, Dennis Ritchie, Brian Kernighan, Douglas McIlroy, and Joe Ossanna...
operating systems, OS/2
OS/2
OS/2 is a computer operating system, initially created by Microsoft and IBM, then later developed by IBM exclusively. The name stands for "Operating System/2," because it was introduced as part of the same generation change release as IBM's "Personal System/2 " line of second-generation personal...
1.x, and Windows used this mode. Windows 3.0
Windows 3.0
Windows 3.0, a graphical environment, is the third major release of Microsoft Windows, and was released on 22 May 1990. It became the first widely successful version of Windows and a rival to Apple Macintosh and the Commodore Amiga on the GUI front...
was able to run real mode programs in 16-bit protected mode. Windows 3.0
Windows 3.0
Windows 3.0, a graphical environment, is the third major release of Microsoft Windows, and was released on 22 May 1990. It became the first widely successful version of Windows and a rival to Apple Macintosh and the Commodore Amiga on the GUI front...
, when switching to protected mode, decided to preserve the single privilege level model that was used in real mode, which is why Windows applications and DLLs can hook interrupts and do direct hardware access. That lasted through the Windows 9x
Windows 9x
Windows 9x is a generic term referring to a series of Microsoft Windows computer operating systems produced since 1995, which were based on the original and later modified Windows 95 kernel...
series. If a Windows 1.x or 2.x program is written properly and avoids segment arithmetic, it will run the same way in both real and protected modes. Windows programs generally avoid segment arithmetic because Windows implements a software virtual memory scheme, moving program code and data in memory when programs are not running, so manipulating absolute addresses is dangerous; programs should only keep handle
Smart pointer
In computer science, a smart pointer is an abstract data type that simulates a pointer while providing additional features, such as automatic garbage collection or bounds checking. These additional features are intended to reduce bugs caused by the misuse of pointers while retaining efficiency...
s to memory blocks when not running. Starting an old program while Windows 3.0 is running in protected mode triggers a warning dialog, suggesting to either run Windows in real mode or to obtain an updated version of the application. Updating well-behaved programs using the MARK utility with the MEMORY parameter avoids this dialog. It is not possible to have some GUI programs running in 16-bit protected mode and other GUI programs running in real mode. In Windows 3.1 real mode disappeared.
Today, 16-bit protected mode is still used for running applications, e.g. DPMI compatible DOS extender
DOS extender
A DOS extender is a computer software program which enables software to run under a protected mode environment even though the host operating system is only capable of operating in real mode....
programs (through virtual DOS machine
Virtual DOS machine
Virtual DOS machine is Microsoft's technology that allows running legacy DOS and 16-bit Windows programs on Intel 80386 or higher computers when there is already another operating system running and controlling the hardware.-Overview:...
s) or Windows 3.x applications (through the Windows on Windows
Windows on Windows
In computing, Windows on Windows - commonly referred to by its acronym WOW or WoW - is a software component of 32-bit versions of the Microsoft Windows NT family of operating systems that provides limited support for running legacy Win16 applications - applications written for Windows 3.x...
subsystem) and certain classes of device driver
Device driver
In computing, a device driver or software driver is a computer program allowing higher-level computer programs to interact with a hardware device....
s (e.g. for changing the screen-resolution using BIOS functionality) in OS/2 2.0 and later, all under control of a 32-bit kernel.
See also
- Assembly languageAssembly languageAn assembly language is a low-level programming language for computers, microprocessors, microcontrollers, and other programmable devices. It implements a symbolic representation of the machine codes and other constants needed to program a given CPU architecture...
- Intel
- Ring (computer security)Ring (computer security)In computer science, hierarchical protection domains, often called protection rings, are a mechanism to protect data and functionality from faults and malicious behaviour . This approach is diametrically opposite to that of capability-based security.Computer operating systems provide different...
- x86 assembly languageX86 assembly languagex86 assembly language is a family of backward-compatible assembly languages, which provide some level of compatibility all the way back to the Intel 8008. x86 assembly languages are used to produce object code for the x86 class of processors, which includes Intel's Core series and AMD's Phenom and...
External links
- Protected Mode Basics
- Introduction to Protected-Mode
- Overview of the Protected Mode Operations of the Intel Architecture
- Intel 64 and IA-32 Architectures Software Developer's Manuals
- TurboIRC.COM tutorial to enter protected mode from DOS
- Protected Mode Overview and Tutorial
- Code Project Protected Mode Tutorial

