
Network tap
Encyclopedia
A network tap is a hardware device which provides a way to access the data flowing across a computer network
. In many cases, it is desirable for a third party to monitor the traffic between two points in the network. If the network between points A and B consists of a physical cable, a "network tap" may be the best way to accomplish this monitoring. The network tap has (at least) three ports: an A port, a B port, and a monitor port. A tap inserted between A and B passes all traffic through unimpeded, but also copies that same data to its monitor port, enabling a third party to listen.
Network taps are commonly used for network intrusion detection system
s, VoIP recording
, network probes, RMON
probes, packet sniffer
s, and other monitoring and collection devices and software that require access to a network segment
. Taps are used in security applications because they are non-obtrusive, are not detectable on the network (having no physical or logical address), can deal with full-duplex and non-shared networks, and will usually pass through traffic even if the tap stops working or loses power.
or vampire tap
. Some vendors have phrases for which tap is an acronym; however, those are most likely bacronyms.
The monitored traffic is sometimes referred to as the pass-through traffic, while the ports that are used for monitoring are the monitor ports. There may also be an aggregation port for full-duplex traffic, wherein the "A" traffic is aggregated with the "B" traffic, resulting in one stream of data /packets for monitoring the full-duplex communication. The packets must be aligned into a single stream using a time-of-arrival algorithm.
Vendors will tend to use terms in their marketing such as breakout, passive, aggregating, regeneration, inline power, and others. Common meanings will be discussed later. Unfortunately, vendors do not use such terms consistently. Before buying any products, be sure to understand the available features, and check with vendors or read the product literature closely to figure out how marketing terms correspond to reality. All of the "Vendor Terms" are common within the industry and have real definitions and are valuable points of consideration when buying a tap device.
A distributed tap is a set of network taps which report to a centralized monitoring system or packet analyzer.
or port-bonding
is recommended to avoid packet loss to the monitoring tools.
A filterable tap, that provides advanced filtering, can selectively pass data, based on application, VLAN ID, or other parameters, to the 1-Gigabit port for deep analysis and monitoring, including IDS requirements.
Filtered access is also the best way to focus on business-critical traffic, or other specific areas of your network. At higher speeds, network traffic analysis cannot be performed using the older "capture and decode everything" philosophy. In this type of environment, focused access is the best way to enable traffic analysis, and often is the only way.
Any filterable tap you consider must have a simple user interface for easy setup and management. Furthermore, it must be able to collect the Layer 1 and Layer 2 data, while still allowing for auto saving, and easy access to data by graphing programs. Such a tap can be part of a strategy to monitor for essential metrics, such as frame errors and corrupted frames in IPv6.
(i.e., piece of a network) was very easy—just connect the monitoring device as you would any other host, and enable promiscuous mode
. Modern network technologies tend to be switched
, meaning that devices are connected using point-to-point links. If a monitoring device is connected to such a network, it will only see its own traffic. The network tap allows the monitoring device to view the contents of a point-to-point link.
Modern network technologies are often full-duplex, meaning that data can travel in both directions at the same time. If a network link allows 100 Mbit/s of data to flow in each direction at the same time, this means that the network really allows 200 Mbit/s of aggregate throughput
. This can present a problem for monitoring technologies if they have only one monitor port. Therefore, network taps for full-duplex technologies usually have two monitor ports, one for each half of the connection. The listener must use channel bonding
or link aggregation
to merge the two connections into one aggregate interface to see both halves of the traffic. Other monitoring technologies do not deal well with the full-duplex problem.
Once a network tap is in place, the network can be monitored without interfering with the network itself. Other network monitoring solutions require in-band changes to network devices, which means that monitoring can impact the devices being monitored.
Once a tap is in place, a monitoring device can be connected to it as-needed without impacting the monitored network.
Some taps have multiple output ports, or multiple pairs of output ports for full-duplex, to allow more than one device to monitor the network at the tap point. These are often called regeneration taps.
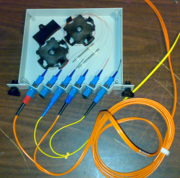
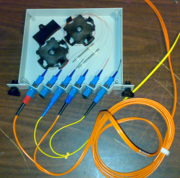 Some taps, particularly fiber taps, can use no power and no electronics at all for the pass-through and monitor portion of the network traffic. This means that the tap should never suffer any kind of electronics failure or power failure that results in a loss of network connectivity. One way this can work, for fiber-based network technologies, is that the tap divides the incoming light using a simple physical apparatus into two outputs, one for the pass-through, one for the monitor. This can be called a passive tap. Other taps use no power or electronics for the pass-through, but do use power and electronics for the monitor port. These can also be referred to as passive. Fiber-based taps are of limited usage, non-orthogonal photon fiber network can not be taped at all.
Some taps, particularly fiber taps, can use no power and no electronics at all for the pass-through and monitor portion of the network traffic. This means that the tap should never suffer any kind of electronics failure or power failure that results in a loss of network connectivity. One way this can work, for fiber-based network technologies, is that the tap divides the incoming light using a simple physical apparatus into two outputs, one for the pass-through, one for the monitor. This can be called a passive tap. Other taps use no power or electronics for the pass-through, but do use power and electronics for the monitor port. These can also be referred to as passive. Fiber-based taps are of limited usage, non-orthogonal photon fiber network can not be taped at all.
Some taps operate at the physical layer
of the OSI model
rather than the data link
layer. For example, they work with multi-mode fiber rather than 1000BASE-SX. This means that they can work with most data link network technologies that use that physical media, such as ATM and some forms of Ethernet. Network taps that act as simple optical splitters, sometimes called passive taps (although that term is not used consistently) can have this property.
Some network taps offer both duplication of network traffic for monitoring devices and SNMP services. Most major network tap manufacturers offer taps with remote management through Telnet, HTTP, or SNMP interfaces. Such network tap hybrids can be helpful to network managers who wish to view baseline performance statistics without diverting existing tools. Alternatively, SNMP alarms generated by managed taps can alert network managers to link conditions that merit examination by analyzers to intrusion detection systems.
Some taps get some of their power (i.e., for the pass-through) or all of their power (i.e., for both pass-through and monitor) from the network itself. These can be referred to as having inline power.
Some taps can also reproduce low-level network errors, such as short frames, bad CRC or corrupted data.
Network taps can require channel bonding
on monitoring devices to get around the problem with full-duplex discussed above. Vendors usually refer to this as aggregation as well.
Putting a network tap into place will disrupt the network being monitored for a short time. It's better than taking a network down multiple times to deploy a monitoring tool though. Establishing good guidelines for placement of network taps is recommended procedure.
Monitoring large networks using network taps can require a lot of monitoring devices. High end networking devices often allow ports to be enabled as mirror ports
which is a software network tap. While any free port can be configured as a mirror port, software taps require configuration and place load on the network devices.
Even fully passive network taps introduce new points of failure into the network. There are several ways that taps can cause problems and this should be considered when creating a tap architecture. Consider non-powered taps for optical-only environments or throwing star network tap for copper 100BT. This allows you to modify the intelligent aggregation taps that may be in use and avoids any complications when upgrading from 100 megabit to gigabit to 10 gigabit. Redundant
power supplies are highly recommended.
The simplest type of monitoring is logging in to an interesting device and running programs or commands that show performance statistics and other data. This is the cheapest way to monitor a network, and is highly appropriate for small networks. However, it does not scale well to large networks. It can also impact the network being monitored; see observer effect
.
Another way to monitor devices is to use a remote management protocol such as SNMP
to ask devices about their performance. This scales well, but is not necessarily appropriate for all types of monitoring. The inherent problems with SNMP are the polling effect. Many vendors have alleviated this by using intelligent polling schedulers, but this may still affect the performance of the device being monitored. It also opens up a host of potential security problems.
Another method to monitor networks is by enable promiscuous mode
on the monitoring host, and connecting it to a shared segment
. This works well with older LAN
technologies such as 10BASE-T
Ethernet
, FDDI, and token ring. On such networks, any host can automatically see what all other hosts were doing by enabling promiscuous mode. However, modern switched
network technologies such as those used on modern Ethernets provide, in effect, point-to-point links between pairs of devices, so it is hard for other devices to see traffic.
Another method to monitor networks is to use port mirroring
(called "SPAN", for Switched Port Analyzer, by Cisco
, and given other names by some other vendors) on routers and switches
. This is a low-cost alternative to network taps, and solves many of the same problems. However, not all routers and switches support port mirroring and, on those that do, using port mirroring can affect the performance of the router or switch. These technologies may also be subject to the problem with full-duplex described elsewhere in this article, and there are often limits for the router or switch on how many pass-through sessions can be monitored, or how many monitor ports (generally two) can monitor a given session.
Computer network
A computer network, often simply referred to as a network, is a collection of hardware components and computers interconnected by communication channels that allow sharing of resources and information....
. In many cases, it is desirable for a third party to monitor the traffic between two points in the network. If the network between points A and B consists of a physical cable, a "network tap" may be the best way to accomplish this monitoring. The network tap has (at least) three ports: an A port, a B port, and a monitor port. A tap inserted between A and B passes all traffic through unimpeded, but also copies that same data to its monitor port, enabling a third party to listen.
Network taps are commonly used for network intrusion detection system
Network intrusion detection system
A Network Intrusion Detection System is an intrusion detection system that tries to detect malicious activity such as denial of service attacks, port scans or even attempts to crack into computers by Network Security Monitoring of network traffic.A NIDS reads all the incoming packets and tries to...
s, VoIP recording
VoIP recording
Voice over Internet Protocol recording is a subset of telephone recording or voice logging, first used by call centers and now being used by all types of businesses...
, network probes, RMON
RMON
The Remote Network MONitoring MIB was developed by the IETF to support monitoring and protocol analysis of LANs. The original version focused on OSI Layer 1 and Layer 2 information in Ethernet and Token Ring networks...
probes, packet sniffer
Packet sniffer
A packet analyzer is a computer program or a piece of computer hardware that can intercept and log traffic passing over a digital network or part of a network...
s, and other monitoring and collection devices and software that require access to a network segment
Network segment
A network segment is a portion of a computer network. The nature and extent of a segment depends on the nature of the network and the device or devices used to interconnect end stations.-Ethernet:...
. Taps are used in security applications because they are non-obtrusive, are not detectable on the network (having no physical or logical address), can deal with full-duplex and non-shared networks, and will usually pass through traffic even if the tap stops working or loses power.
Terminology
The term network tap is analogous to phone tapTelephone tapping
Telephone tapping is the monitoring of telephone and Internet conversations by a third party, often by covert means. The wire tap received its name because, historically, the monitoring connection was an actual electrical tap on the telephone line...
or vampire tap
Vampire tap
A vampire tap is a device for physically connecting a station to a network that uses 10BASE5 cabling...
. Some vendors have phrases for which tap is an acronym; however, those are most likely bacronyms.
The monitored traffic is sometimes referred to as the pass-through traffic, while the ports that are used for monitoring are the monitor ports. There may also be an aggregation port for full-duplex traffic, wherein the "A" traffic is aggregated with the "B" traffic, resulting in one stream of data /packets for monitoring the full-duplex communication. The packets must be aligned into a single stream using a time-of-arrival algorithm.
Vendors will tend to use terms in their marketing such as breakout, passive, aggregating, regeneration, inline power, and others. Common meanings will be discussed later. Unfortunately, vendors do not use such terms consistently. Before buying any products, be sure to understand the available features, and check with vendors or read the product literature closely to figure out how marketing terms correspond to reality. All of the "Vendor Terms" are common within the industry and have real definitions and are valuable points of consideration when buying a tap device.
A distributed tap is a set of network taps which report to a centralized monitoring system or packet analyzer.
New filterable tap technology
A new type of tap, or network access point, is now available. This new type of tap is called a "filterable" tap. It is especially valuable in the 10 Gigabit environment because 10-Gigabit test equipment is very expensive. Some taps, like those from several vendors, offer the ability to utilize less expensive and more widely available 1-Gigabit monitoring and analysis tools with these 10 Gigabit networks. When used in this fashion, some form of load-balancingLoad balancing (computing)
Load balancing is a computer networking methodology to distribute workload across multiple computers or a computer cluster, network links, central processing units, disk drives, or other resources, to achieve optimal resource utilization, maximize throughput, minimize response time, and avoid...
or port-bonding
Link aggregation
Link aggregation or trunking or link bundling or Ethernet/network/NIC bonding or NIC teaming are computer networking umbrella terms to describe various methods of combining multiple network connections in parallel to increase throughput beyond what a single connection could sustain, and to provide...
is recommended to avoid packet loss to the monitoring tools.
A filterable tap, that provides advanced filtering, can selectively pass data, based on application, VLAN ID, or other parameters, to the 1-Gigabit port for deep analysis and monitoring, including IDS requirements.
Filtered access is also the best way to focus on business-critical traffic, or other specific areas of your network. At higher speeds, network traffic analysis cannot be performed using the older "capture and decode everything" philosophy. In this type of environment, focused access is the best way to enable traffic analysis, and often is the only way.
Any filterable tap you consider must have a simple user interface for easy setup and management. Furthermore, it must be able to collect the Layer 1 and Layer 2 data, while still allowing for auto saving, and easy access to data by graphing programs. Such a tap can be part of a strategy to monitor for essential metrics, such as frame errors and corrupted frames in IPv6.
Advantages and features
Older network technologies tended to be shared. Connecting a monitoring device to a shared network segmentNetwork segment
A network segment is a portion of a computer network. The nature and extent of a segment depends on the nature of the network and the device or devices used to interconnect end stations.-Ethernet:...
(i.e., piece of a network) was very easy—just connect the monitoring device as you would any other host, and enable promiscuous mode
Promiscuous mode
In computer networking, promiscuous mode or promisc mode is a mode for a network interface controller that causes the NIC to pass all traffic it receives to the central processing unit rather than just passing frames the NIC is intended to receive...
. Modern network technologies tend to be switched
Network switch
A network switch or switching hub is a computer networking device that connects network segments.The term commonly refers to a multi-port network bridge that processes and routes data at the data link layer of the OSI model...
, meaning that devices are connected using point-to-point links. If a monitoring device is connected to such a network, it will only see its own traffic. The network tap allows the monitoring device to view the contents of a point-to-point link.
Modern network technologies are often full-duplex, meaning that data can travel in both directions at the same time. If a network link allows 100 Mbit/s of data to flow in each direction at the same time, this means that the network really allows 200 Mbit/s of aggregate throughput
Throughput
In communication networks, such as Ethernet or packet radio, throughput or network throughput is the average rate of successful message delivery over a communication channel. This data may be delivered over a physical or logical link, or pass through a certain network node...
. This can present a problem for monitoring technologies if they have only one monitor port. Therefore, network taps for full-duplex technologies usually have two monitor ports, one for each half of the connection. The listener must use channel bonding
Channel bonding
Channel bonding is a computer networking arrangement in which two or more network interfaces on a host computer are combined for redundancy or increased throughput....
or link aggregation
Link aggregation
Link aggregation or trunking or link bundling or Ethernet/network/NIC bonding or NIC teaming are computer networking umbrella terms to describe various methods of combining multiple network connections in parallel to increase throughput beyond what a single connection could sustain, and to provide...
to merge the two connections into one aggregate interface to see both halves of the traffic. Other monitoring technologies do not deal well with the full-duplex problem.
Once a network tap is in place, the network can be monitored without interfering with the network itself. Other network monitoring solutions require in-band changes to network devices, which means that monitoring can impact the devices being monitored.
Once a tap is in place, a monitoring device can be connected to it as-needed without impacting the monitored network.
Some taps have multiple output ports, or multiple pairs of output ports for full-duplex, to allow more than one device to monitor the network at the tap point. These are often called regeneration taps.
Some taps operate at the physical layer
Physical layer
The physical layer or layer 1 is the first and lowest layer in the seven-layer OSI model of computer networking. The implementation of this layer is often termed PHY....
of the OSI model
OSI model
The Open Systems Interconnection model is a product of the Open Systems Interconnection effort at the International Organization for Standardization. It is a prescription of characterizing and standardizing the functions of a communications system in terms of abstraction layers. Similar...
rather than the data link
Data link
In telecommunication a data link is the means of connecting one location to another for the purpose of transmitting and receiving information. It can also refer to a set of electronics assemblies, consisting of a transmitter and a receiver and the interconnecting data telecommunication circuit...
layer. For example, they work with multi-mode fiber rather than 1000BASE-SX. This means that they can work with most data link network technologies that use that physical media, such as ATM and some forms of Ethernet. Network taps that act as simple optical splitters, sometimes called passive taps (although that term is not used consistently) can have this property.
Some network taps offer both duplication of network traffic for monitoring devices and SNMP services. Most major network tap manufacturers offer taps with remote management through Telnet, HTTP, or SNMP interfaces. Such network tap hybrids can be helpful to network managers who wish to view baseline performance statistics without diverting existing tools. Alternatively, SNMP alarms generated by managed taps can alert network managers to link conditions that merit examination by analyzers to intrusion detection systems.
Some taps get some of their power (i.e., for the pass-through) or all of their power (i.e., for both pass-through and monitor) from the network itself. These can be referred to as having inline power.
Some taps can also reproduce low-level network errors, such as short frames, bad CRC or corrupted data.
Disadvantages and problems
Network taps require additional hardware, so are not as cheap as technologies that use capabilities that are built-in to the network. They are easier to manage and normally provide more data than some network devices though.Network taps can require channel bonding
Channel bonding
Channel bonding is a computer networking arrangement in which two or more network interfaces on a host computer are combined for redundancy or increased throughput....
on monitoring devices to get around the problem with full-duplex discussed above. Vendors usually refer to this as aggregation as well.
Putting a network tap into place will disrupt the network being monitored for a short time. It's better than taking a network down multiple times to deploy a monitoring tool though. Establishing good guidelines for placement of network taps is recommended procedure.
Monitoring large networks using network taps can require a lot of monitoring devices. High end networking devices often allow ports to be enabled as mirror ports
Port mirroring
Port Mirroring is used on a network switch to send a copy of network packets seen on one switch port to a network monitoring connection on another switch port. This is commonly used for network appliances that require monitoring of network traffic, such as an intrusion-detection system...
which is a software network tap. While any free port can be configured as a mirror port, software taps require configuration and place load on the network devices.
Even fully passive network taps introduce new points of failure into the network. There are several ways that taps can cause problems and this should be considered when creating a tap architecture. Consider non-powered taps for optical-only environments or throwing star network tap for copper 100BT. This allows you to modify the intelligent aggregation taps that may be in use and avoids any complications when upgrading from 100 megabit to gigabit to 10 gigabit. Redundant
Redundancy (engineering)
In engineering, redundancy is the duplication of critical components or functions of a system with the intention of increasing reliability of the system, usually in the case of a backup or fail-safe....
power supplies are highly recommended.
Comparison to other monitoring technologies
Various monitoring approaches can be used, depending on the network technology and the monitoring objective:The simplest type of monitoring is logging in to an interesting device and running programs or commands that show performance statistics and other data. This is the cheapest way to monitor a network, and is highly appropriate for small networks. However, it does not scale well to large networks. It can also impact the network being monitored; see observer effect
Observer effect
Observer effect may refer to:* Observer effect , the impact of observing a process while it is running* Observer effect , the impact of observing a physical system...
.
Another way to monitor devices is to use a remote management protocol such as SNMP
Simple Network Management Protocol
Simple Network Management Protocol is an "Internet-standard protocol for managing devices on IP networks. Devices that typically support SNMP include routers, switches, servers, workstations, printers, modem racks, and more." It is used mostly in network management systems to monitor...
to ask devices about their performance. This scales well, but is not necessarily appropriate for all types of monitoring. The inherent problems with SNMP are the polling effect. Many vendors have alleviated this by using intelligent polling schedulers, but this may still affect the performance of the device being monitored. It also opens up a host of potential security problems.
Another method to monitor networks is by enable promiscuous mode
Promiscuous mode
In computer networking, promiscuous mode or promisc mode is a mode for a network interface controller that causes the NIC to pass all traffic it receives to the central processing unit rather than just passing frames the NIC is intended to receive...
on the monitoring host, and connecting it to a shared segment
Network segment
A network segment is a portion of a computer network. The nature and extent of a segment depends on the nature of the network and the device or devices used to interconnect end stations.-Ethernet:...
. This works well with older LAN
Län
Län and lääni refer to the administrative divisions used in Sweden and previously in Finland. The provinces of Finland were abolished on January 1, 2010....
technologies such as 10BASE-T
10BASE-T
Ethernet over twisted pair technologies use twisted-pair cables for the physical layer of an Ethernet computer network. Other Ethernet cable standards employ coaxial cable or optical fiber. Early versions developed in the 1980s included StarLAN followed by 10BASE-T. By the 1990s, fast, inexpensive...
Ethernet
Ethernet
Ethernet is a family of computer networking technologies for local area networks commercially introduced in 1980. Standardized in IEEE 802.3, Ethernet has largely replaced competing wired LAN technologies....
, FDDI, and token ring. On such networks, any host can automatically see what all other hosts were doing by enabling promiscuous mode. However, modern switched
Network switch
A network switch or switching hub is a computer networking device that connects network segments.The term commonly refers to a multi-port network bridge that processes and routes data at the data link layer of the OSI model...
network technologies such as those used on modern Ethernets provide, in effect, point-to-point links between pairs of devices, so it is hard for other devices to see traffic.
Another method to monitor networks is to use port mirroring
Port mirroring
Port Mirroring is used on a network switch to send a copy of network packets seen on one switch port to a network monitoring connection on another switch port. This is commonly used for network appliances that require monitoring of network traffic, such as an intrusion-detection system...
(called "SPAN", for Switched Port Analyzer, by Cisco
Cisco Systems
Cisco Systems, Inc. is an American multinational corporation headquartered in San Jose, California, United States, that designs and sells consumer electronics, networking, voice, and communications technology and services. Cisco has more than 70,000 employees and annual revenue of US$...
, and given other names by some other vendors) on routers and switches
Network switch
A network switch or switching hub is a computer networking device that connects network segments.The term commonly refers to a multi-port network bridge that processes and routes data at the data link layer of the OSI model...
. This is a low-cost alternative to network taps, and solves many of the same problems. However, not all routers and switches support port mirroring and, on those that do, using port mirroring can affect the performance of the router or switch. These technologies may also be subject to the problem with full-duplex described elsewhere in this article, and there are often limits for the router or switch on how many pass-through sessions can be monitored, or how many monitor ports (generally two) can monitor a given session.
See also
- Packet snifferPacket snifferA packet analyzer is a computer program or a piece of computer hardware that can intercept and log traffic passing over a digital network or part of a network...
- Port mirroringPort mirroringPort Mirroring is used on a network switch to send a copy of network packets seen on one switch port to a network monitoring connection on another switch port. This is commonly used for network appliances that require monitoring of network traffic, such as an intrusion-detection system...
- VACLVACLVLAN Access Control Lists provide access control for all packets that are bridged within a VLAN or that are routed into or out of a VLAN. Unlike regular Cisco IOS access control lists that are configured on router interfaces and applied on routed packets only, VACLs apply to all packets...
- Telena SPA
- NetOptics

